Most organizations have a clear process for buying IT equipment. There are approvals. Budgets. Asset tags. Deployment checklists. Everything is tracked carefully when devices enter the business.
Then, one day, those same devices are retired.
Laptops are replaced. Servers are decommissioned. Storage arrays are pulled from racks. Equipment leaves desks, closets, and data centers. And this is where many organizations make a quiet but costly assumption.
That once an asset is no longer in use, it is no longer a risk.
In reality, retired IT equipment does not disappear when it powers down or leaves the building. Data remains. Ownership remains. Liability remains. In many cases, regulatory responsibility remains as well.
This is the gap that IT Asset Disposition exists to close.
ITAD is not about getting rid of old hardware. It is about controlling what happens next. Who touches retired assets. Where they go. What happens to the data they contain. How risk is reduced rather than shifted somewhere else and forgotten about.
For years, IT asset disposal was treated as an operational afterthought. Something handled informally, outsourced quickly, or bundled into recycling programs with little visibility. That approach no longer works.
Today’s IT environments are data-heavy, highly regulated, and widely distributed. Devices move across regions. Storage exists in many forms. Refresh cycles are faster. The consequences of getting disposal wrong are higher. Which means the end of the IT lifecycle has become just as important as the beginning.
This article explains what IT Asset Disposition really is, why it matters more than most organizations realize, and how a structured ITAD program protects businesses from data exposure, compliance failures, and environmental risk, while also creating opportunities for reuse and value recovery.
If IT equipment enters your organization through a system, it should leave through one too. That system is ITAD.
What is ITAD?
IT Asset Disposition, commonly referred to as ITAD, is the structured process used to manage IT equipment once it reaches the end of its active use inside an organization. At its core, ITAD ensures three things happen reliably and in the right order.
First, all data contained on retired assets is securely removed or destroyed in a verifiable way.
Second, any remaining value in the equipment or its components is recovered where possible.
Third, assets that cannot be reused are disposed of responsibly, in compliance with environmental and regulatory requirements.
A proper ITAD program governs what happens to assets from the moment they are retired until their final outcome is documented and closed. That includes collection, tracking, data handling, decisions about reuse or destruction, and proof that stands up to audit or customer review.
Why ITAD matters more than most organizations realize
For many organizations, IT asset disposition feels low risk. Devices are old. Systems have been replaced. Access credentials have changed. On the surface, it appears the danger has already passed.
In practice, the opposite is often true.
Retired IT assets frequently represent the highest concentration of unmanaged risk in the entire IT lifecycle. Not because they are actively used, but because they are no longer actively controlled.
Data does not disappear when a device is powered down. Storage media retains information long after systems are decommissioned. In complex environments, especially those with years of layered infrastructure, it is common for assets to contain data that is forgotten, misclassified, or assumed to be gone.
That assumption is where exposure begins.
Many organizations discover this only after an audit, a customer inquiry, or a regulatory review forces them to account for what happened to retired equipment months or even years earlier. At that point, the question is no longer theoretical. It becomes very specific, very quickly.
Where did this asset go?
Who handled it?
Was the data removed?
How do you know?
If those answers are not documented, the organization is left defending intent rather than demonstrating control. Regulators, auditors, and customers tend to prefer the latter.
ITAD also matters because informal disposal practices do not scale.
What works when a team retires a few dozen laptops breaks down when hundreds or thousands of devices move through refresh cycles, office consolidations, or data center transitions. As volumes increase, so does complexity. Different asset types. Different storage formats. Different regulatory requirements across regions.
At that point, risk is no longer about technical capability. It is about governance.
This is why many organizations move away from ad hoc disposal methods as they grow. Not because they lack good intentions, but because intention does not substitute for structure. A disciplined ITAD program provides consistency, traceability, and proof, even as asset volumes and geographic spread increase.
There is also a financial dimension that is often overlooked.
Without a structured approach, reusable equipment is frequently destroyed too early or written off entirely. Components with recoverable value are treated as waste simply because there is no process to evaluate them properly. Over time, this creates a pattern where organizations absorb unnecessary losses while still carrying residual risk.
ITAD matters because it closes all of these gaps at once. It turns a vague end-of-life moment into a controlled process with defined outcomes, documented decisions, and measurable results.
What happens when ITAD is done incorrectly
Most ITAD failures do not start with negligence. They start with shortcuts. A device is assumed to be wiped. A pallet is handed off without full documentation. A recycler is trusted without downstream visibility.
Nothing immediately breaks. So everything feels fine. Until it isn’t.
When ITAD is done incorrectly, problems tend to surface later, often detached from the original decision that caused them. By then, assets have changed hands, records are incomplete, and institutional memory has moved on. The organization is left trying to reconstruct events instead of demonstrating control.
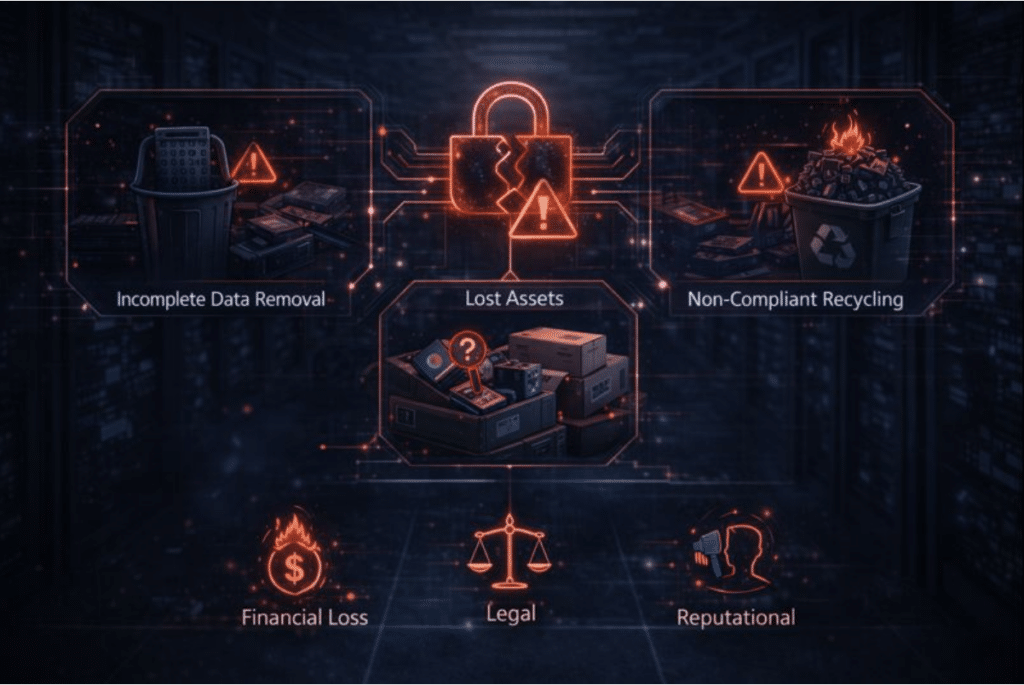
Common ITAD failures
The most frequent ITAD breakdowns tend to fall into a few predictable categories.
Incomplete or unverified data removal
Data wiping is performed, but not validated. Logs are missing. Certificates are generic. In some cases, only primary drives are addressed while embedded storage, SSDs, or removable media are overlooked.
Loss of assets during transit or handling
Without a formal chain of custody, assets can be misplaced, mixed, or diverted. This is especially common during office closures, refresh cycles, or large-scale infrastructure changes.
Informal resale or recycling channels
Assets are sold, donated, or recycled through third parties without clear accountability. Downstream handling is assumed rather than proven.
Poor documentation and recordkeeping
Disposition records are incomplete, inconsistent, or difficult to retrieve. When questions arise, there is no single source of truth.
Each of these failures creates exposure on its own. Together, they compound risk quickly.
The real consequences
When ITAD goes wrong, the impact is rarely limited to IT.
From a security standpoint, improperly handled assets increase the likelihood of data exposure. Even a single device with residual data can trigger breach notifications, forensic investigations, and regulatory scrutiny.
From a compliance perspective, the absence of verifiable records is often more damaging than the incident itself. Regulators and auditors focus on whether controls existed, were followed, and can be demonstrated. Intent does not carry much weight without evidence.
There is also reputational impact. Customers and partners expect organizations to manage data responsibly across its entire lifecycle. A disposal-related failure can undermine trust in ways that are difficult to quantify but very real.
And then there is cost.
Fines, legal fees, internal investigations, and lost productivity add up quickly. At the same time, organizations often discover that valuable equipment was destroyed unnecessarily, while risk was still retained elsewhere.
(Which is about as inefficient as it sounds.)
This is why mature organizations treat ITAD failures as governance failures, not operational mistakes. The issue is not that something went wrong once. It is that the system allowed it to go unnoticed.
A structured ITAD program exists to prevent these outcomes by design. It replaces assumption with verification and informal handling with documented control.
The evolution of IT asset disposition
IT Asset Disposition did not start as a strategic discipline. For a long time, it was treated as cleanup.
Early ITAD practices were largely reactive. Equipment reached the end of its useful life, and the primary concern was removing it from the building. Recycling vendors were engaged. Storage rooms were cleared. The assumption was that disposal marked the end of responsibility.
That assumption no longer holds.
From electronics recycling to risk management
As organizations became more data-driven, the nature of IT assets changed. Devices were no longer just hardware. They became containers for sensitive information, business logic, customer records, and regulated data.
At the same time, IT environments grew more complex.
Servers multiplied. Storage formats diversified. Infrastructure spread across offices, regions, and data centers. Remote work accelerated the distribution of endpoints well beyond traditional corporate boundaries.
In this environment, disposal stopped being a logistical task and became a risk-management problem.
Organizations began to recognize that what mattered most was not how quickly equipment was removed, but how securely and transparently it was handled from retirement to final disposition. This shift is what transformed ITAD from recycling into a lifecycle control function.
Regulation, scale, and the end of informality
Regulatory pressure played a major role in this evolution.
Data protection laws introduced clear expectations around data handling, documentation, and accountability. It was no longer enough to believe data had been removed. Organizations were expected to prove it.
At the same time, asset volumes increased. Refresh cycles shortened. Mergers, acquisitions, and infrastructure modernization programs became more common. Informal disposal methods that might have worked at small scale began to fail under real-world conditions.
What emerged was a new model of ITAD.
One that treats retired assets as governed objects rather than waste. One that integrates security, compliance, financial recovery, and environmental responsibility into a single process. One that produces records designed for audits, not just internal reassurance.
(This is usually the point where teams realize disposal was quietly one of their least controlled processes.)
Modern ITAD exists because the environment demanded it. The risks grew. The expectations hardened. And the cost of getting it wrong became too high to ignore.
Why data security is the core of ITAD
Strip ITAD down to its essentials, and one priority sits above everything else.
Data protection.
IT assets are not neutral objects. They are storage vessels. Even when systems are retired, powered down, or physically removed, the data they contain often remains intact. In many cases, it remains readable with minimal effort.
This is why data security is not one component of ITAD. It is the reason ITAD exists.
A retired laptop can still hold employee records. A decommissioned server can still contain customer data. A storage array pulled from a rack may carry years of transactional history.
None of that risk disappears just because the asset is no longer productive.
In fact, retired assets are often more dangerous than active ones. Active systems are monitored, patched, and governed by access controls. Retired devices sit outside those safeguards. They fall into transitional states where oversight is weaker and assumptions replace verification.
This is where many organizations get caught off guard.
They focus heavily on protecting data while systems are live, then relax controls at the point of retirement. From a risk perspective, that is backwards. The moment data leaves a controlled production environment is the moment it requires the most discipline.
A proper ITAD program treats retired assets as high-risk objects until proven otherwise. Data must be securely removed or destroyed using approved methods. The outcome must be verified. And the process must be documented in a way that stands up to scrutiny.
Without that structure, organizations are left hoping that nothing was missed.
(Hope is not a control. Auditors are particularly unimpressed by it.)
This is also why ITAD decisions often involve security and compliance teams, not just IT operations. Data protection obligations do not end at decommissioning. They extend until data is rendered permanently inaccessible and that outcome can be demonstrated.
When ITAD is designed around data security first, everything else aligns more easily. Compliance follows. Audit readiness improves. Reuse decisions become safer. Environmental goals can be pursued without introducing new exposure.
When data security is treated as secondary, the entire program becomes fragile.
Data Protection and Regulatory Compliance
For most organizations, regulatory compliance becomes the forcing function that turns ITAD from a nice-to-have into a requirement.
Data protection laws do not stop applying when a device is retired. In many cases, they become more relevant. Regulators care about how data is handled across its entire lifecycle, including how it is removed, destroyed, or rendered inaccessible at the end.
This is where informal disposal practices tend to fall apart.
A spreadsheet that says “disposed” is not the same as proof. A verbal assurance from a vendor is not the same as evidence. And a policy that exists on paper does not help much if the execution cannot be demonstrated.
How ITAD supports regulatory compliance
A structured ITAD program provides the controls and documentation regulators expect to see.
This typically includes clear procedures for identifying data-bearing assets, applying approved data sanitization methods, and recording outcomes in a consistent and retrievable way. The goal is not perfection. The goal is defensibility.
When regulators or auditors ask how retired assets were handled, organizations need to be able to answer with facts, not assumptions.
That is why ITAD aligns closely with widely recognized frameworks and regulations, including GDPR for personal data protection, HIPAA for healthcare information, and industry guidance such as NIST and IEEE for data sanitization. These standards share a common theme. Data must be protected until it is verifiably gone.
ITAD provides the operational bridge between those requirements and real-world execution.
Compliance is about proof, not intent
One of the most common misunderstandings around compliance is the belief that good intentions carry weight. They do not.
Audits focus on whether controls exist, whether they were followed, and whether outcomes can be demonstrated after the fact. This is where ITAD documentation becomes critical.
Certificates of data erasure or destruction, chain of custody records, asset tracking logs, and disposition reports all serve the same purpose. They provide objective evidence that data protection obligations were met.
Without those records, organizations are often left reconstructing events long after the fact, relying on memory or fragmented systems. That is not a strong position to be in during a regulatory review.
(If you have ever tried to answer an audit question that starts with “Can you show us…”, you already know how this ends.)
A mature ITAD program treats compliance as an output of good process, not a separate activity. When data handling is designed correctly from the start, compliance follows naturally.
Data erasure vs. physical data destruction
One of the most common points of confusion in ITAD is the difference between data erasure and physical data destruction.
Both are valid. Both are used regularly. And both serve very different purposes.
Understanding when to use each approach is essential for balancing data security, compliance, sustainability, and value recovery.
Data erasure explained
Data erasure is the process of securely overwriting data on a storage device so that it can no longer be recovered. When performed correctly and verified, erasure renders data permanently inaccessible while allowing the device itself to remain intact.
This matters because intact devices can be reused.
Erased drives can be redeployed internally, refurbished for resale, or harvested for components. From a lifecycle perspective, erasure supports both security and sustainability goals. Data is protected, and hardware remains in circulation.
The key phrase here is “when performed correctly.”
Effective data erasure follows recognized standards, applies to all addressable storage areas, and produces verifiable results. Logs, reports, and certificates are not administrative extras. They are the proof that erasure actually occurred.
Without verification, erasure is an assumption. And assumptions do not hold up well under scrutiny.
Physical data destruction explained
Physical data destruction takes a different approach.
Instead of overwriting data, the storage media itself is rendered unusable. Drives are shredded, crushed, or otherwise destroyed so that data cannot be accessed again. Once destruction occurs, reuse is no longer possible.
This method is typically used when:
- Assets are too old or damaged for reuse
- Regulatory or internal policies require destruction
- Storage devices cannot be reliably erased
- Risk tolerance is extremely low
Physical destruction offers clarity. There is no question about whether the data is gone. The tradeoff is that it eliminates any remaining asset value and ends the lifecycle immediately.
Choosing the right approach
The decision between erasure and destruction should not be arbitrary.
A mature ITAD program evaluates asset condition, data sensitivity, regulatory requirements, and reuse potential before determining the appropriate method. In many environments, both approaches are used side by side, depending on asset type and risk profile.
What matters most is not which method is chosen, but how well it is executed and documented.
Verification is non-negotiable. Whether data is erased or destroyed, organizations need clear evidence of the outcome. Certificates, logs, and traceable records close the loop and provide defensible proof during audits or investigations.
When erasure and destruction are applied deliberately and transparently, ITAD becomes a tool for control rather than a source of uncertainty.
Chain of custody and accountability
Data security does not end once an asset leaves the building. In many ways, that is when risk increases.
Chain of custody is the mechanism that keeps retired IT assets visible, controlled, and accountable as they move through the ITAD process. It answers a simple but critical question at every step.
Who has the asset right now?
What chain of custody means in ITAD
In the context of ITAD, chain of custody refers to the documented tracking of assets from the moment they are collected through transport, processing, and final disposition.
This includes:
- Asset identification and tagging
- Recorded handoffs between parties
- Secure transport and storage
- Controlled processing environments
- Documented final outcomes
Each step creates a record. Together, those records form a traceable history that shows where an asset was, who handled it, and what was done to it.
This matters because retired assets are most vulnerable when they are in motion. During pickups, relocations, consolidations, and decommissioning events, devices pass through multiple hands and locations. Without clear custody controls, assets can be lost, mixed, or mishandled without immediate detection.
Chain of custody exists to prevent that.
Why accountability reduces risk
From a risk perspective, chain of custody does two things at once.
First, it reduces the likelihood of loss or diversion. When assets are tracked and reconciled at each stage, discrepancies are easier to spot and address early.
Second, it creates defensible proof.
If an organization is asked to demonstrate how a specific device was handled, chain of custody records provide concrete answers. Not estimates. Not recollections. Actual documentation.
This is especially important in regulated environments, where organizations may be required to prove not only that data was removed, but that assets were protected throughout the entire disposition process.
Without chain of custody, even well-executed data erasure or destruction can be undermined. The work may have been done correctly, but the organization cannot confidently prove that the right asset went through the right process.
(Which tends to be a problem only when someone asks. And someone eventually asks.)
A mature ITAD program treats accountability as a design requirement, not an afterthought. Chain of custody is built into how assets are collected, transported, processed, and closed out. The result is fewer blind spots and far fewer uncomfortable questions later.
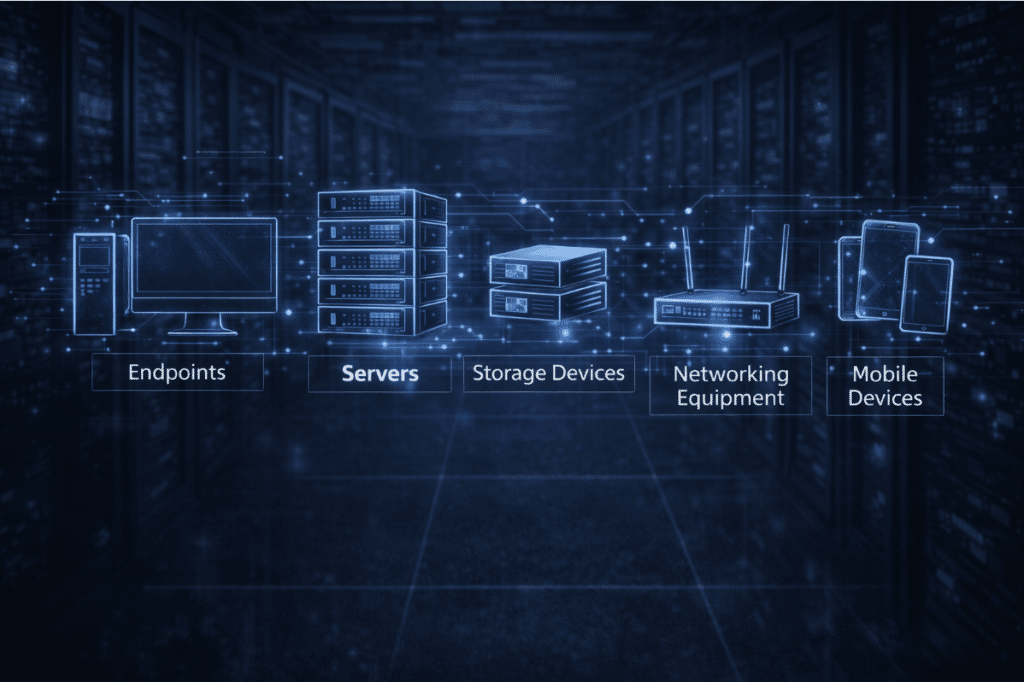
What types of assets are included in ITAD?
ITAD applies to far more than office laptops and aging servers.
As technology has spread across homes, stores, networks, and customer environments, the scope of IT asset disposition has expanded alongside it. A modern ITAD program must account for where devices live, how they are used, and what kind of data or system access they carry, not just what category they fall into.
At Reconext, ITAD programs commonly span the following asset categories.
Consumer electronics
Consumer electronics represent one of the most widely distributed and frequently refreshed asset groups.
These devices often move between users, locations, and environments, including remote and home settings. While they may appear low risk on the surface, they frequently contain cached credentials, synced data, and access to enterprise systems long after their primary use ends.
A structured ITAD approach ensures consumer electronics are collected, processed, and documented consistently, with secure data handling and appropriate reuse or recovery decisions.
Consumer electronics ITAD services
Enterprise network and data storage equipment
Enterprise network and data storage assets sit at the center of organizational data risk.
This category includes servers, storage systems, and network infrastructure that support core business operations. These assets often contain sensitive customer data, system configurations, credentials, and historical records, making their disposition especially critical.
ITAD programs for enterprise network and data storage equipment must support secure data removal, verifiable outcomes, and scalable execution across large volumes and complex environments.
Enterprise network and data storage ITAD
Point-of-sale equipment
Point-of-sale equipment introduces a unique combination of scale, distribution, and sensitivity.
POS devices often process transaction data and operate across large, geographically dispersed retail environments. When these systems are refreshed, relocated, or retired, inconsistent handling can quickly create compliance and data protection gaps.
A disciplined ITAD program ensures POS equipment is recovered securely, data is handled correctly, and assets are processed in a way that supports both regulatory requirements and operational efficiency.
Customer premises equipment
Customer premises equipment presents a different kind of challenge.
These assets often spend much of their lifecycle outside direct corporate control, deployed at customer locations. Even so, they can store configuration data, credentials, and access information that must be protected when devices are returned, upgraded, or decommissioned.
ITAD programs for customer premises equipment focus on secure recovery, validation, and appropriate reuse or disposition, ensuring assets re-enter controlled processes without introducing new risk.
Customer premises equipment ITAD
Data center decommissioning assets
Data center decommissioning represents ITAD at its most complex and high stakes.
Entire environments may be dismantled at once, involving thousands of assets, multiple storage formats, and overlapping compliance requirements. Execution must remain controlled, auditable, and secure throughout the process.
In this context, ITAD is not a background activity. It is a central mechanism for protecting data, maintaining chain of custody, and enabling reuse and value recovery during large-scale infrastructure transitions.
IoT devices
IoT devices extend ITAD into environments that traditional IT processes often overlook.
These assets may operate in homes, offices, retail locations, or industrial settings, collecting data and connecting to enterprise systems in the background. Because of their number and dispersion, they are easy to miss during retirement or replacement.
A mature ITAD program includes IoT devices based on their data exposure and connectivity, ensuring they are securely handled rather than quietly forgotten.
Mobile devices
Mobile devices combine high data sensitivity with constant movement.
Smartphones and related devices often contain personal data, authentication tokens, and access to enterprise applications. Their portability and frequent upgrades make informal disposal especially risky.
ITAD programs for mobile devices prioritize secure data handling, verifiable outcomes, and consistent processing at scale.
Why this scope matters
ITAD works best when scope is defined by risk and reality, not by outdated assumptions about what counts as “IT.”
When organizations limit ITAD to a narrow set of assets, exposure tends to migrate elsewhere. When scope reflects how technology is actually deployed and used, ITAD becomes a durable control that scales with the business.
(Which is often when teams realize how much their environment has changed without anyone formally noticing.)
How a modern ITAD program works
One of the biggest mistakes organizations make with ITAD is treating it as a single event. Something you do at the end. A pickup. A cleanout. A checkbox.
In reality, a modern ITAD program works more like a system. It starts before assets are physically removed and continues until outcomes are verified, documented, and closed.
This shift matters because most ITAD risk does not come from any one step. It comes from the gaps between steps.
ITAD as an integrated process
A mature ITAD program is designed to operate across functions and timelines, not in isolation.
Retirement decisions trigger security considerations. Security decisions affect reuse options. Reuse decisions influence environmental outcomes and financial recovery.
When these elements are handled independently, inconsistencies creep in. When they are handled as part of a single process, control improves across the board.
In practical terms, a modern ITAD program typically includes:
- Pre-disposition planning, where assets are identified and scoped
- Secure collection and transport under controlled conditions
- Data handling using approved, verifiable methods
- Evaluation for reuse, refurbishment, or recovery
- Responsible recycling for assets that cannot be reused
- Centralized documentation and reporting to close the loop
Each stage builds on the previous one. Skipping steps or compressing them into a single action is where most failures originate.
Designed for scale, not exception handling
Another defining characteristic of modern ITAD is that it is designed for scale.
Many organizations initially manage disposition through informal processes because volumes are low. That approach tends to break down quietly as the environment grows. More devices. More locations. More refresh cycles. More regulatory exposure.
A modern ITAD program assumes variability and volume from the start. It is built to handle hundreds or thousands of assets without relying on manual tracking, individual judgment calls, or heroics from a single team.
Visibility from start to finish
Perhaps the most important change in modern ITAD is visibility.
Instead of assets disappearing into a handoff and reappearing later as a report, a structured ITAD program maintains visibility throughout the process. Assets are tracked. Status is known. Outcomes are confirmed.
This visibility is what allows organizations to answer difficult questions with confidence.
What happened to this asset?
When was the data removed?
Who handled it?
How was the outcome verified?
Those answers should be available without reconstructing events or chasing emails from months ago.
When ITAD is treated as a system rather than a task, it stops being a source of uncertainty. It becomes a controlled extension of the IT lifecycle.
Core components of a modern ITAD program
Once ITAD is treated as a system rather than a one-off task, its core components become easier to see.
A modern ITAD program is not defined by a single tool or activity. It is defined by how several elements work together to reduce risk, preserve value, and produce defensible outcomes. When one component is weak or missing, the entire program becomes fragile.
The most effective ITAD programs are built on four foundational components.
Security and data protection
Security is the backbone of ITAD.
This includes identifying all data-bearing assets, applying appropriate data sanitization methods, and verifying outcomes before assets move on to the next stage. Security controls must account for different device types, storage formats, and risk profiles rather than assuming a one-size-fits-all approach.
What matters most is not speed, but certainty. Data must be rendered permanently inaccessible, and the organization must be able to prove that result later.
This is where structured IT Asset Disposition services matter most, because they replace informal handling with repeatable, auditable controls.
Compliance and documentation
Compliance is the visible output of good ITAD process.
A modern program produces consistent documentation that shows what happened to each asset, when it happened, and how outcomes were verified. This includes asset tracking records, data erasure or destruction certificates, and chain of custody logs that can be retrieved when needed.
The goal is not to generate paperwork for its own sake. The goal is to make compliance routine rather than reactive.
When documentation is centralized and standardized, audits become confirmations instead of investigations.
(Which is the version everyone prefers.)
Value recovery and reuse
ITAD is often viewed purely through a risk lens, but value recovery is a critical component of mature programs.
Many retired assets still have usable life, either as complete devices or as components. A modern ITAD program evaluates assets for refurbishment, redeployment, or resale before defaulting to destruction or recycling.
This approach extends product life, reduces waste, and helps offset IT refresh costs without compromising security or compliance.
Value recovery works only when security and verification are handled first. When those foundations are in place, reuse becomes a controlled decision rather than a gamble.
Environmental responsibility
Environmental responsibility is not a separate track. It is an outcome of disciplined ITAD execution.
Assets that cannot be reused must be processed through compliant recycling channels with proper downstream controls. Materials should be recovered responsibly, and disposal practices must meet regulatory and environmental standards across regions.
A modern ITAD program treats recycling as the final step, not the primary objective. Reuse comes first. Recovery follows. Disposal is the last option.
This approach aligns ITAD with broader sustainability goals without introducing additional risk or complexity.
Refurbishment, reuse, and asset value recovery
One of the quieter benefits of a well-designed ITAD program is that it changes how organizations think about retired assets.
Instead of defaulting to disposal, assets are evaluated. Instead of being written off immediately, they are assessed for what they can still contribute. This shift does not reduce security. When done correctly, it improves it.
Refurbishment and reuse only work when they are built on verified data handling and controlled processes.
Extending the life of IT assets
Many devices reach the end of their primary use long before they reach the end of their functional life.
Laptops may no longer meet performance requirements for certain roles but remain perfectly usable elsewhere. Servers may be retired due to refresh cycles rather than failure. Components within larger systems may still hold value even when the system as a whole is no longer needed.
A mature ITAD program identifies these opportunities deliberately.
Assets are inspected, tested where appropriate, and classified based on condition and reuse potential. Devices that meet defined criteria can be refurbished and redeployed internally, sold through controlled channels, or harvested for components.
This approach reduces unnecessary destruction while maintaining full control over data security and compliance.
Value recovery without compromising control
Value recovery is not about squeezing every dollar out of old hardware. It is about avoiding avoidable loss.
When assets are destroyed prematurely, organizations absorb the full cost of replacement while still having invested time and resources into the original equipment. Over time, this creates a pattern where refresh cycles become more expensive than they need to be.
By contrast, structured value recovery allows organizations to recapture some of that investment without introducing new risk. The key is sequencing.
Data is handled first. Verification comes next. Only then does reuse or resale enter the conversation.
When that order is reversed, reuse becomes risky. When it is respected, reuse becomes a controlled extension of the lifecycle.
(This is also why informal resale channels tend to fail. They optimize for speed, not certainty.)
Supporting broader lifecycle and sustainability goals
Refurbishment and reuse also support environmental objectives.
Extending the life of devices reduces demand for new manufacturing, conserves materials, and lowers the environmental footprint associated with IT refresh cycles. These benefits are real, but they only materialize when reuse decisions are made responsibly.
A modern ITAD program treats reuse as a governed outcome, not an exception. It aligns financial recovery, environmental responsibility, and data protection rather than forcing tradeoffs between them.
Electronic waste management as a final step
Recycling is often the first thing people think of when they hear ITAD. In a mature program, it is the last step.
Electronic waste management plays an important role, but only after every reasonable opportunity for secure reuse and value recovery has been exhausted. Treating recycling as the default outcome usually means assets are being retired too early or without proper evaluation.
A modern ITAD program reverses that logic.
Recycling as an outcome, not a shortcut
When assets are no longer suitable for reuse due to age, condition, or policy requirements, responsible recycling becomes essential. At this stage, the goal is to recover materials safely and compliantly, without introducing downstream risk.
This includes ensuring that recycling partners meet environmental and regulatory standards, that materials are processed through approved channels, and that proper documentation exists to confirm final disposition.
What matters most is visibility.
Organizations need to know where assets go after they leave their custody, how they are processed, and whether disposal practices align with legal and environmental obligations across regions. Informal or opaque recycling arrangements often create more risk than they remove.
Downstream accountability matters
One of the most overlooked aspects of electronic waste management is downstream accountability.
Even after assets are handed off for recycling, organizations can remain responsible for how those materials are handled. Improper disposal, export violations, or non-compliant processing can still create legal and reputational exposure.
This is why electronic waste management must be integrated into the broader ITAD framework rather than treated as a standalone service. Chain of custody, documentation, and verified outcomes matter just as much at the end of the process as they do at the beginning.
Aligning recycling with ITAD objectives
When recycling is handled correctly, it supports both risk reduction and sustainability goals.
Materials are recovered responsibly. Environmental impact is reduced. Compliance requirements are met. And organizations can demonstrate that assets were managed appropriately through their entire lifecycle.
This alignment is difficult to achieve when recycling is bolted on at the end. It becomes far more effective when it is designed into the ITAD program from the start.
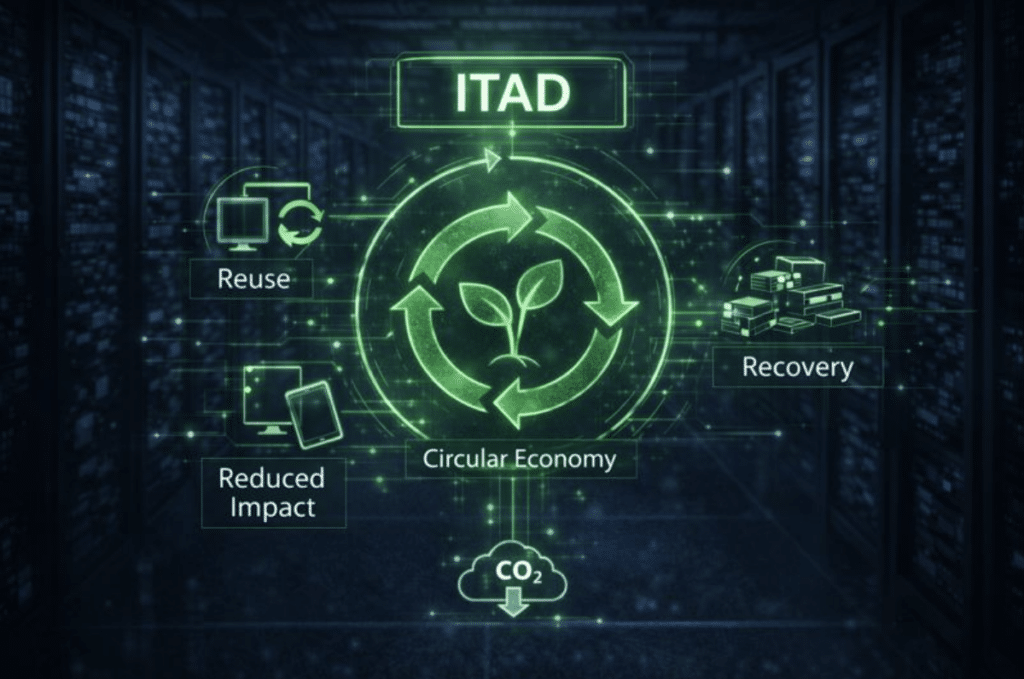
ITAD, sustainability, and the circular economy
Sustainability is often discussed as a parallel initiative. Something adjacent to IT operations. Something reported on, but managed elsewhere. ITAD changes that dynamic.
When IT asset disposition is structured correctly, sustainability becomes an operational outcome rather than a separate program. Decisions about reuse, recovery, and disposal directly influence environmental impact, whether that impact is measured or not.
ITAD and the circular economy
The circular economy is built on a simple idea. Keep products and materials in use for as long as possible. ITAD is one of the few places in the IT lifecycle where this principle can be applied at scale.
By prioritizing refurbishment, redeployment, and component recovery, ITAD extends the useful life of equipment that would otherwise be destroyed prematurely. This reduces demand for new manufacturing, conserves raw materials, and lowers the environmental footprint associated with frequent refresh cycles.
Recycling still plays a role, but only after reuse options have been evaluated and exhausted. In a circular model, recycling is not success. It is the fallback.
This is where disciplined ITAD programs make a measurable difference. They create the conditions for circular outcomes by controlling data risk first, then enabling safe reuse and recovery.
ITAD and corporate sustainability reporting
Sustainability goals increasingly come with reporting obligations.
Organizations are expected to show progress, not just intent. That requires data. And much of that data is generated, or lost, during asset disposition.
A structured ITAD program produces tangible metrics that support sustainability reporting, including asset reuse rates, material recovery volumes, and verified disposal outcomes. These metrics allow organizations to move beyond estimates and into defensible reporting.
Just as importantly, ITAD provides transparency.
When asset flows are tracked and outcomes are documented, organizations can demonstrate how environmental goals are being supported in practice. This transparency strengthens ESG reporting and reduces the risk of overstated or unsupported claims.
Environmental responsibility without added risk
One of the persistent myths around sustainability is that it requires tradeoffs. In ITAD, the opposite is often true.
When data security, compliance, and chain of custody are handled properly, sustainability outcomes become easier to achieve, not harder. Assets can be reused safely. Materials can be recovered responsibly. Disposal can be documented clearly.
The key is integration. When sustainability is layered onto ITAD as an afterthought, it creates tension. When it is built into how assets are evaluated and processed, it reinforces the entire program.
This is how ITAD moves from risk mitigation to long-term value creation.
Who uses ITAD and why
ITAD is not limited to a single industry or company size. It becomes relevant anywhere IT assets store data, support regulated processes, or operate at scale.
What changes across organizations is not whether ITAD is needed, but why it becomes unavoidable.
Large enterprises and global organizations
Large enterprises typically adopt ITAD because scale exposes weakness.
As asset volumes grow and environments spread across regions, informal disposal practices stop working. Devices move between offices. Storage systems are refreshed on fixed schedules. Assets cross borders. Regulatory requirements vary by geography.
At that point, the risk is not that something unusual will happen. It is that something ordinary will happen at scale.
Enterprises rely on ITAD to create consistency across locations, enforce data handling standards, and maintain documentation that can withstand audits across jurisdictions. Without structured ITAD, governance breaks down unevenly and quietly.
Healthcare organizations
Healthcare organizations face some of the strictest data protection obligations.
Medical devices, endpoints, servers, and storage systems often contain protected health information. That data remains regulated even after the equipment is retired.
ITAD in healthcare environments is driven by the need to ensure that patient data is rendered permanently inaccessible and that the organization can demonstrate how that outcome was achieved. Chain of custody, verified sanitization, and defensible records are not optional. They are required.
In these environments, ITAD is often as much a compliance function as an IT function.
Financial services and regulated industries
Financial institutions, insurance providers, and other regulated industries face similar pressures.
Assets may contain customer financial data, transaction records, authentication credentials, and internal system information. Disposal failures create exposure not only to regulators but also to customers and counterparties.
ITAD provides a structured way to manage this risk by ensuring data is handled correctly, assets are tracked, and outcomes are documented. For many regulated organizations, ITAD becomes a necessary extension of their broader risk management framework.
Retail and distributed environments
Retailers and other distributed businesses face a different challenge.
Point-of-sale systems, kiosks, edge devices, and local infrastructure are deployed across hundreds or thousands of locations. Assets are refreshed frequently and often handled locally.
Without centralized ITAD controls, disposal practices vary by site. Devices may be stored, reused, or discarded inconsistently. Data exposure becomes difficult to detect until it is too late.
Retail organizations rely on ITAD to impose consistent standards across distributed environments and to regain visibility over assets that would otherwise fall outside central control.
Service providers and technology companies
Service providers, telecoms, and technology companies often manage assets that operate outside their own facilities.
Customer premises equipment, mobile devices, and IoT assets may spend most of their lifecycle deployed in the field. When these assets are returned, upgraded, or decommissioned, they must re-enter a controlled disposition process.
ITAD helps these organizations manage return flows securely, verify data handling, and determine appropriate reuse or disposal without introducing new risk during transitions.
ITAD within the IT asset lifecycle
ITAD is most effective when it is treated as a formal phase of the IT asset lifecycle rather than a separate activity.
Most organizations invest heavily in procurement, deployment, and maintenance. Controls are strongest when assets are productive. As assets approach retirement, those controls often weaken. That is the gap ITAD is designed to close.
When ITAD is integrated into lifecycle planning, retirement becomes a governed event rather than an afterthought. Assets are identified before they leave service. Data-bearing components are scoped correctly. Disposition decisions are aligned with security, compliance, and sustainability objectives.
This lifecycle view reduces surprises. It also improves coordination between IT, security, compliance, procurement, and operations teams, all of whom have a stake in how assets are retired.
Organizations that treat ITAD as part of lifecycle management tend to experience fewer incidents, fewer audit issues, and less friction during large-scale transitions.
Why organizations partner with ITAD specialists
Most organizations do not handle ITAD entirely in-house. The reason is not lack of capability. It is the difficulty of maintaining consistent controls at scale.
As asset volumes increase and environments become more complex, ITAD requires specialized processes, tooling, and experience. Secure data handling, custody tracking, verification, and downstream compliance must all work together across locations and asset types.
For many organizations, building and maintaining that infrastructure internally is inefficient and risky. Partnering with ITAD specialists allows them to transfer execution to teams that operate these processes continuously.
This does not remove responsibility. It provides expertise, scale, and repeatability that are difficult to achieve through ad hoc internal efforts.
Common misconceptions about ITAD
Despite its importance, ITAD is often misunderstood. One common misconception is that ITAD is the same as electronics recycling. Recycling is one possible outcome, but it is not the purpose of ITAD.
Another misconception is that data wiping alone is sufficient. Without verification and documentation, wiping is an assumption, not a control.
Some organizations also believe ITAD is only necessary for large enterprises. In reality, smaller organizations often face greater risk because they rely more heavily on informal disposal practices.
Finally, there is a belief that ITAD is purely an operational concern. In practice, it intersects with security, compliance, finance, and sustainability. Treating it as an isolated task limits its effectiveness.
Getting started with an ITAD strategy
Organizations looking to strengthen their ITAD approach do not need to start with tools or vendors. They need to start with visibility.
Key questions include:
Which retired assets contain data
How data is currently removed or destroyed
Whether outcomes are verified and documented
How assets are tracked after leaving service
What happens to assets that are reused or recycled
Gaps in these areas usually indicate reliance on assumptions rather than controls.
From there, organizations can define scope, establish standards, and determine whether internal processes are sufficient or whether specialist support is required. The goal is consistency.
ITAD as a strategic safeguard and opportunity
IT Asset Disposition is no longer a back-office function.
It is a safeguard that protects data, supports compliance, reduces environmental impact, and preserves value across the IT lifecycle. As technology continues to spread across locations, devices, and environments, the risks associated with retirement will only increase.
Organizations that treat ITAD as a structured, auditable process are better positioned to manage that risk. They replace assumption with proof. They align security with sustainability. They close the lifecycle rather than leaving it open-ended.
That is what modern ITAD is designed to do.