Getting FDA approval for the design and commissioning of healthcare devices marks a major milestone in healthcare manufacturing. Today marks the beginning of a regulatory lifecycle that you must actively manage and oversee.
To ensure compliance with this, the FDA established the Total Product Life Cycle, which requires you to have a comprehensive plan for the entire lifecycle of devices. The IT asset disposition (ITAD) for healthcare manufacturers is the formal process that manufacturers follow for safe, compliant, and efficient handling.
This article explores the best practices of retiring old healthcare devices and software, challenges to avoid, and how to choose the right ITAD partner.
Key Takeaways
- Healthcare IT asset disposition manages end-of-life IT assets in a secure and compliant manner.
- Professional vendors possess NAID AAA, e-Stewards, ISO, NIST, and other industry certifications that demonstrate adherence to industry standards.
What is IT Asset Disposition for Healthcare Manufacturers?
Most healthcare device manufacturers assume that the end user is responsible for ITAD. If you thought the same, that’s a wrong assumption. Even without the regulation of the FDA to enforce ITAD, you would be risking a lot if you fail to integrate ITAD in your operations.
Think about it: when an unauthorized third party gets hold of your proprietary software, your intellectual property is at risk. Similarly, if a device you manufactured is refurbished and put to use without your knowledge, you risk huge liability if it causes any damage.
Healthcare ITAD is the framework that helps you safeguard your intellectual property, monitor usage of your devices, and avoid penalties from bodies such as FDA or HIPAA. In healthcare environments and large health systems, that same framework also supports data protection for regulated assets and helps healthcare organizations and providers securely handle sensitive information through retirement.
IT asset disposition is a coordinated process. That is why your organization needs a responsible person in charge of it. This person coordinates the disposition process with the end user (your customers) and the ITAD partner.
The IT asset disposition process is highly customizable. ITAD providers will advise you on the best approach, choosing from reuse, recycle, or deconstruction. For instance, data-bearing devices like hard drives and solid-state drives that contain critical data should be properly destroyed.
Other electronic devices that do not contain sensitive PII data can also be resold to recoup some of their original value and improve financial return.
Impact of FDA Regulations on ITAD Processes
Best practices for general ITAD recommend a structured approach for lifecycle management of healthcare devices. In unregulated industries, vendors have the flexibility to design their management systems however they like.
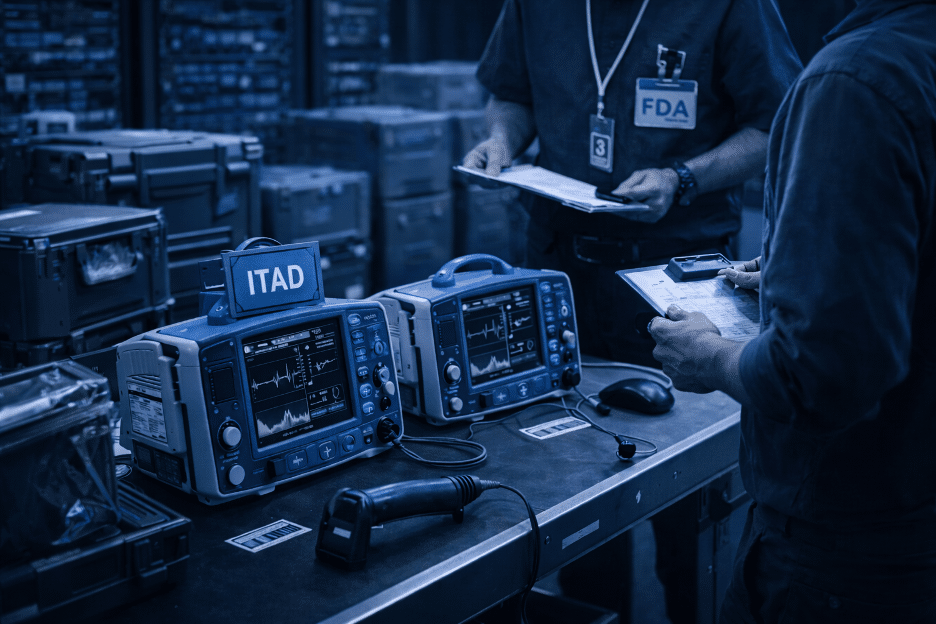
In healthcare manufacturing, the FDA has a Quality Management System Regulation (QMSR) framework that you should follow when curating an ITAD plan. This regulation requires that you have a documented process of how you deconstruct retired assets, support compliant asset disposal, and maintain an audited and documented chain of custody for the same.
Under these regulations, you still have the burden of surveillance if your devices exist without a deconstruction certificate. This surveillance should be proactive, and you must monitor performance, issue recalls, and maintain a valid warranty.
For covered entities and many organizations working under strict security requirements, that level of oversight is essential for regulatory compliance and the protection of patient information across the healthcare industry.
Deconstruction certificates, which ITAD partners provide after a successful IT asset disposition, help you avoid this burden that can be an unbudgeted ITAD expense. On top of this, such documents are useful during compliance audits as proof of successful ITAD.
They also support a detailed chain of documentation that helps demonstrate adherence to HIPAA regulations, compliance standards, and requirements around protected health information and electronic protected health information.
Implementing a Defensible ITAD Strategy
Your top priorities should be data security, chain of custody security, and environmental responsibility. If you design your strategy around these priorities, you will have a plan that lets you stick to ITAD best practices and the law.
Integrate ITAD into Quality Management System (QMS)
Starting February 2026, the FDA aligned with ISO 13485:2016, a general framework for medical devices quality management systems.
What this means for you is that the FDA needs stricter documentation and better lifecycle management across your product lines. Integrating ITAD into the QMS can help you achieve these requirements.
An integrated ITAD process contains ITAD policies, standardized SOPs, an ITAD partner, and auditing documentation. After creating this process, you need to test it in real workflows and optimize it as needed for continuous improvement.
Once integrated, you end up with an ITAD process that is repeatable and easily auditable.
Establishing Asset Lifecycle Tracking
You need a clear record of a device’s location, status, and ownership from the moment it is produced to its retirement. Asset lifecycle tracking helps you achieve this.
The process of tracking starts with tagging devices. This is where asset tags and unique identifiers such as serial numbers are used to create digital records of devices and strengthen asset management.
Once devices are tagged, it is easier to monitor their performance over time and ensure a secure chain of custody once they come to the end of life transition. Doing all this supports easy value recovery, stronger regulatory compliance, and a simple solution for tracking mobile devices, lab equipment, and other electronic devices moving through retirement.
Standardize Data Sanitization Workflows
The workflows your organization uses for data sanitization need to be standardized and aligned with industry-wide practices for a successful ITAD process. Plus, the guidelines and recommendations by ISO and other bodies mean you will not have to rely on guesswork.
A standard sanitization workflow follows recognized guidelines such as NIST SP 800-88. Under this guideline, we have three levels of data sanitization:
- Clearing: This method overwrites existing data using software techniques.
- Purging: When purging data, advanced techniques like ATA Secure Erase or Cryptographic Erasure are used to make data recovery impossible.
- Destroying: Also known as physical destruction, this sanitization method renders devices incapable of storing data.
The right method of sanitization will depend on the type of device and the data it contains. This includes systems that may store financial data, patient data, and other forms of protected health information. Also, the next stage in the chain of custody will dictate the method you use.
Following NIST SP 800-88 also helps align sanitization workflows with NIST standards so healthcare manufacturers can better ensure data is removed from storage media before reuse, resale, or responsible recycling.
The following table will help you decide the right sanitization approach:
| Device Category | Data Type | Chain of Custody | Recommended Method |
| Non-storage devices (no persistent memory) | General / none | Reuse (internal) | Clearing |
| Clinical devices with limited storage (e.g., temporary patient/session data) | General (non-identifiable) | Reuse/resale | Clearing |
| Clinical devices with persistent storage (e.g., diagnostics, monitoring systems) | Sensitive (PHI) | Reuse (internal controlled environment) | Purging |
| Clinical devices with persistent storage | Sensitive (PHI) | Resale / third-party reuse | Purging |
| IT-integrated medical devices (e.g., workstations, servers, imaging systems) | Sensitive (PHI) | Reuse/resale | Purging |
| Any device category | Sensitive or unknown | Recycling/disposal | Destroying |
Best Practices for Protecting Intellectual Property During ITAD
Intellectual property is among the main reasons for recommending strict ITAD, especially in healthcare manufacturing. Think of the proprietary software that runs your diagnostic devices. In the wrong hands, this intellectual property could be reverse-engineered or sold to competitors.
Another worst-case scenario is when devices containing sensitive data are recalled or traded in but are not decommissioned properly.
Access to this data could expose your company to financial and legal liabilities, especially when patient data or other sensitive information is involved. In some cases, that exposure can contribute to data breaches that disrupt downstream operations and affect patient care.
These scenarios can be avoided by doing the following:
- Choosing certified ITAD partners: Certified ITAD partners commit themselves to the highest ITAD standards in the industry.
- Maintaining a strict chain of custody: Safe ownership and handling of retired devices ensures data is protected from unwarranted access.
- Using certified sanitization methods: Use the above table to choose the right data erasure method to avoid IP theft and lower the risk of data breaches.
- Get Certificate of Deconstruction (CoD): After each deconstruction, always ask for this certificate, which certifies that data was successfully destroyed as part of a verified destruction process.
Intellectual property is not limited to finished products. It also resides in manufacturing processes and in-progress designs. As a result, IT asset disposition must extend to systems like the Manufacturing Execution System (MES) that store production data.
In some cases, secure decommissioning also affects the handling of electronic devices that contain valuable components or precious metals, which makes controlled downstream processing more important.
What to Look for in a Healthcare Manufacturer ITAD Partner
In healthcare IT asset disposition, there are standards that ITAD partners must meet to be considered compliant and professional. All this starts with data security.
The National Association of Information Destruction (NAID) AAA Certification is considered the gold standard that your ITAD partner must possess. This certification is important because certified vendors are regularly trained and audited. If you want your data protected, pick vendors with this certification.
Other certifications, such as e-Stewards and R2v3, are also indicators of compliance and professionalism. However, these certifications are less about data security and more about sustainable ITAD and responsible recycling, which is equally important. They also show that a vendor follows sustainable practices and industry standards.
Environmental compliance is also important when vetting ITAD vendors. Recycling is a common ITAD practice. However, unsustainable recycling leads to lots of e-waste.
Companies that have certifications such as e-Stewards adhere to the highest standards of environmental protection, reduce environmental impact, and support broader sustainability goals.
When evaluating ITAD vendors, you should look for unique value propositions as well. This is because most of them will meet the baseline requirements, making it hard for you to pick one.
Unique value propositions include a value-recovery first approach to ITAD, where the vendor tries to recoup as much of the original value of the item without defaulting to destroying. Another would be comprehensive ITAD handling and aftercare with complete transparency around transport, tracking, sanitization, and final disposition.
Most vendors outline these capabilities on their websites, so browse them before committing. The right partner should also reduce the heavy lifting for your internal team without weakening control.
Get Secure and Compliant ITAD Services
Healthcare manufacturers need a strict and solid ITAD strategy to avoid data security issues, adhere to environmental guidelines, and maximize asset value. In a highly regulated industry like healthcare, the need for compliance is critical. Evaluate your ITAD strategy against these best practices and find the loopholes you need fixed.
If you are unsure where to start, contact Reconext, and we will help you decommission those retired assets sitting unattended in storage.
FAQs
What is the risk of using a standard recycler instead of a certified ITAD partner?
Standard recyclers often focus on scrap value rather than data security. For a healthcare manufacturer, this creates a high risk of data remnants or proprietary software surviving on the secondary market, leading to HIPAA breaches or the loss of intellectual property.
How is data destruction verified for healthcare manufacturing assets?
Verification is provided through a Serialized Certificate of Destruction (CoD). This document maps the specific serial number of a medical device or hard drive to a timestamped event of data erasure or physical destruction, providing a defensible audit trail that supports audit readiness.
Can manufacturers recover value from retired IT assets?
Yes. Professional ITAD programs include value recovery or remarketing for assets that no longer contain sensitive data. This allows manufacturers to offset the cost of the compliance program by reselling sanitized components or refurbished hardware and improving financial return.