Data center migrations are often presented as infrastructure projects. In practice, they are moments of exposure.
They disrupt systems that may have been running quietly for years. They force long-standing assumptions into the open. They involve not just technology, but people, process, accountability, and trust.
Most migration risks do not come from architecture decisions or destination environments. They emerge when systems are disturbed and physical assets start moving.
Across large enterprise programs, the same pattern appears again and again. The closer a migration gets to physical transition and data center decommissioning, the smaller the margin for error becomes.
Challenge 01: Hidden application and operational dependencies
In mature environments, applications do not operate on their own.
They rely on shared databases, authentication services, schedulers, license servers, and integration points that have evolved over time. Some of these relationships are documented. Many are not. Others exist only in the heads of the people who keep things running.
These dependencies often remain invisible until a system is disturbed.
When servers are powered down, relocated, or restarted in a new environment, assumptions are tested. Something that always worked suddenly does not. A service comes online, but downstream processes fail quietly. Reporting jobs stop running. Authentication behaves differently than expected.
In recovery and repair programs, this is a familiar pattern. The act of touching a system reveals truths that diagrams never captured. Migration exposes systems in the same way.
That is why dependency mapping cannot be treated as a purely technical exercise. It needs input from the people who operate the systems day to day. Ignoring that knowledge creates blind spots that only show up under pressure.
Challenge 02: Maintaining business continuity during transition
Downtime is rarely clean or contained.
Even when maintenance windows are planned, business activity continues. Data changes. Orders arrive. Customers expect consistency. The challenge is not eliminating disruption entirely, but controlling it.
In large operational programs, continuity is achieved through pacing and sequencing. Work is staged. Volume is managed. Temporary parallel states are accepted because they reduce risk.
Migration follows the same logic. Phased transitions and partial cutovers add complexity, but they prevent uncontrolled backlog and recovery work later.
Organizations that optimize for speed alone often pay for it after the move. Stabilization takes longer. Reconciliation becomes harder. Confidence erodes.
Predictability matters more than velocity.
Challenge 03: Protecting data integrity and chain of custody
Data security is often discussed in terms of encryption, access controls, and logical boundaries in the target environment. Those controls matter. They are not where risk peaks.
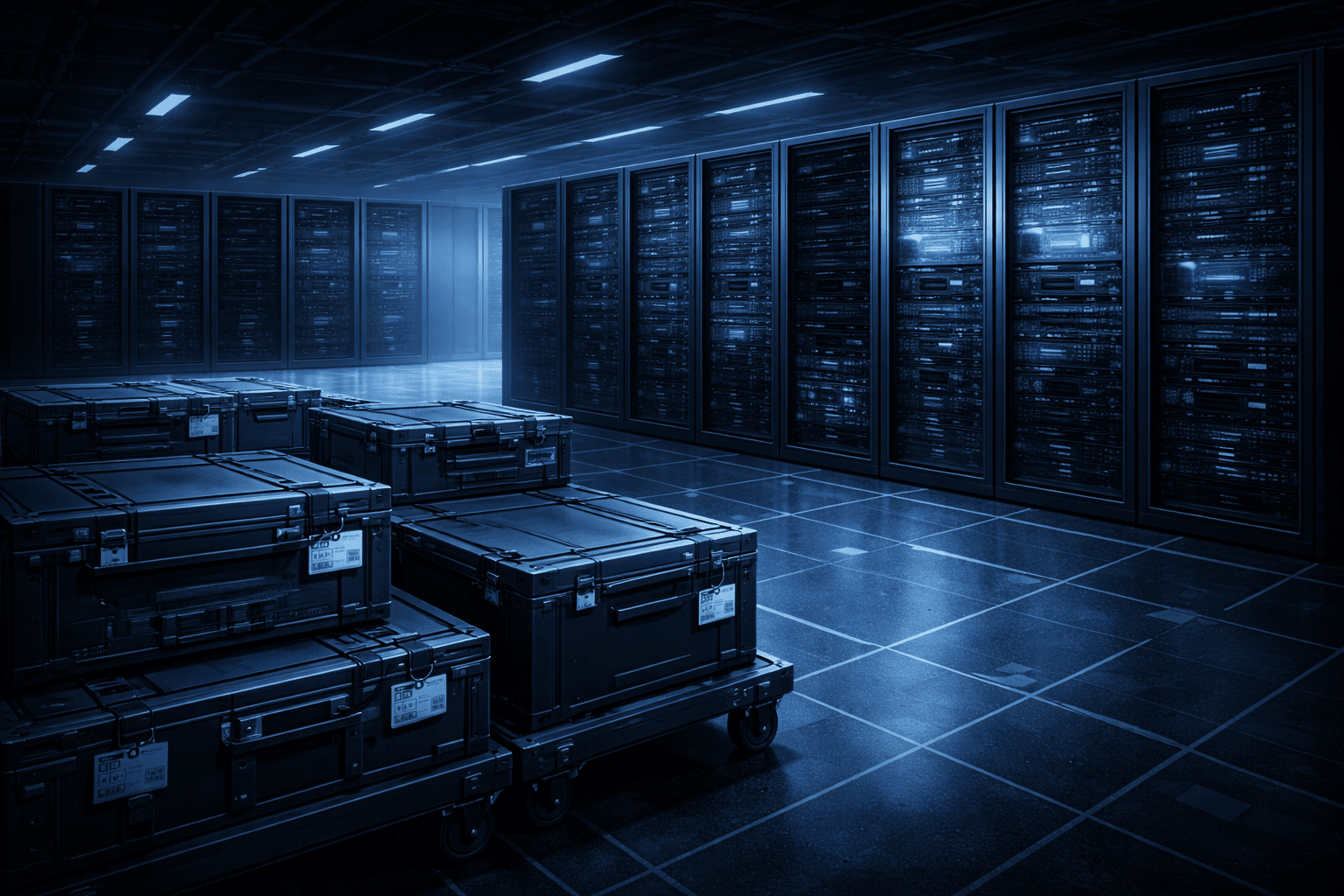
Risk concentrates when data-bearing assets are in motion.
During migration, storage devices are disconnected, transported, staged, wiped, or destroyed. At each step, organizations must be able to answer basic questions clearly and consistently.
- Where was the data at this point in time
- Who had custody
- What controls were applied
- How sanitization or destruction was verified
These questions surface during audits, investigations, and customer reviews. They cannot be answered after the fact if the process was not controlled at the time.
Experience from decommissioning and recovery programs shows that chain of custody is an operational discipline. Logical security does not compensate for physical ambiguity. During migration, physical accountability becomes the foundation of data protection.
We break this down further in our overview of Continuous Custody Intelligence, which explains the six digital and physical layers required to maintain verifiable chain of custody as assets move through transition and decommissioning.
Challenge 04: Infrastructure compatibility and long-tail systems
Not every system is ready to move.
Many environments include long-running platforms that depend on specific hardware, firmware, operating systems, or licensing models. Some are critical. Others persist because replacement cost outweighs perceived risk.
In recovery engineering, this is normal. Teams routinely work with platforms that are ten or twenty years old. The lesson is not that these systems are a mistake. It is that continuity across generations requires intention.
During migration, forcing modernization decisions simply to meet a schedule introduces compounding risk. Infrastructure change and application change collide, increasing the likelihood of failure.
More stable migrations give legacy systems a defined path forward. That might involve temporary hosting, segmentation, or delayed retirement. The key is acknowledging constraints rather than pretending they do not exist.
Migration is about sequencing change, not compressing it.
Challenge 05: Coordination across teams
Data center migration is not owned by one group.
Infrastructure teams manage hardware and networks. Application owners understand workloads. Security and compliance teams define controls. Facilities manage access. Vendors handle logistics. Business leaders care about continuity and cost.
When coordination weakens, migrations slow down. Equipment is removed too early. Systems are assumed to be retired when they are not. Responsibility becomes unclear.
Strong migrations treat coordination as a form of risk control. Ownership is explicit. Timelines are shared. Handoffs are deliberate.
All of these challenges converge during one phase of the migration, when systems are powered down and physical assets are handled.
This matters most during physical transition, where actions are difficult to undo. Once equipment is removed or processed incorrectly, recovery becomes expensive or impossible.
Risk concentrates in decommissioning and physical transition
Risk peaks when equipment starts moving, a critical stage in the Data Center Decommissioning Process where planning meets execution.
Common issues include equipment that is mislabeled or inconsistently tagged, assets mixed during transport, devices removed before workloads are fully transitioned, storage media not wiped correctly, and tracking records that do not line up.
These problems rarely come from carelessness. They arise because physical transition spans teams, locations, and handoffs. Without discipline, control erodes quickly, and once it does, it is difficult to recover.
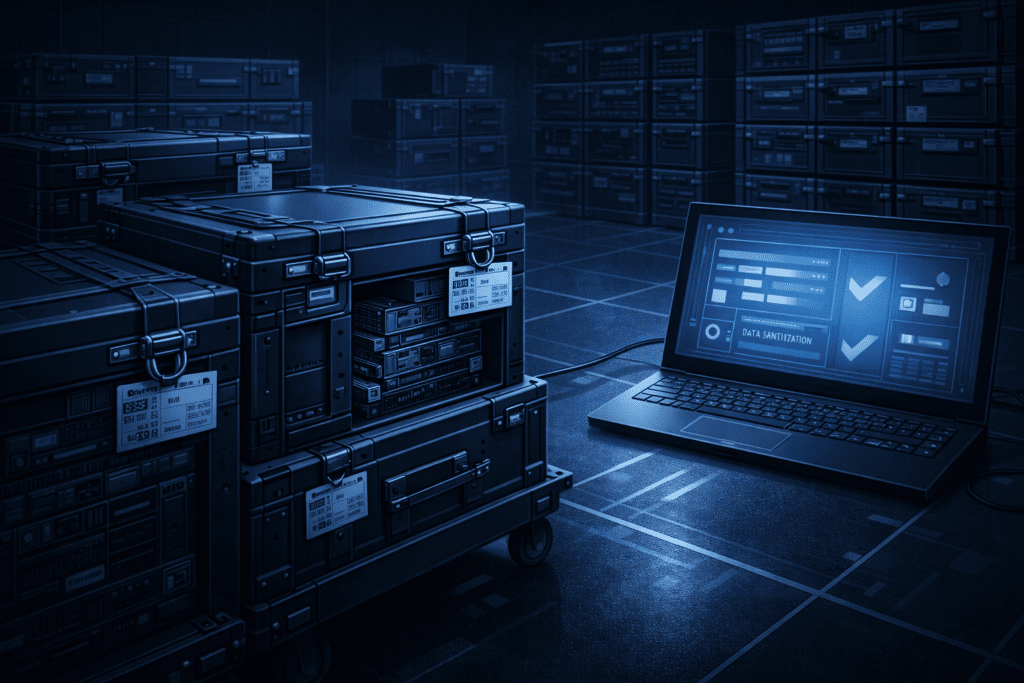
That reality has led some organizations to rethink where risk can be reduced most effectively. In migrations with high regulatory sensitivity, tight timelines, or audit exposure, one of the most reliable ways to preserve control is to limit movement altogether during the earliest stages.
In these cases, data-bearing assets are sanitized and custody is validated on-site, before equipment ever leaves the facility. Reconext supports this approach through secure, portable processing environments, including our box-in-box solution. This allows sanitization, verification, and documentation to occur at the source, while maintaining continuous chain of custody during the most fragile phase of transition.
Decommissioning experience shows why this matters. Assets must be tracked individually, not just in bulk. Data-bearing devices require verified sanitization or destruction. Movement must be traceable from start to finish.
This is the phase auditors focus on most closely, and the phase where mistakes carry lasting consequences.
For teams preparing for this phase, we’ve documented the specific controls, handling steps, and verification requirements used during physical transition and decommissioning to maintain data custody and audit readiness. Read the data center decommissioning checklist.
Reconext’s role during migration
Reconext supports organizations during the most sensitive stages of data center migration. Our focus is on execution, not architecture.
We work where risk concentrates, during physical transition, decommissioning, and data-bearing asset handling.
That work includes secure chain of custody, certified data sanitization or destruction aligned with regulatory requirements, accurate asset tracking throughout movement and processing, and documented traceability that stands up to audit review.
These controls are built from real recovery and decommissioning programs, where proof matters more than promises.
Why migration risk often appears late
One of the hardest aspects of migration risk is that much of it is latent.
Systems appear stable. Documentation looks complete. Plans seem sound. Only when infrastructure is disturbed do hidden dependencies and process gaps surface.
This is why migrations that appear successful at cutover can still create problems months later, often during audits or compliance reviews.
Organizations that navigate migrations well accept this early. They plan not only for the move, but for the scrutiny that follows.
Stability comes from discipline
Data center migration challenges are not primarily technical. They are operational.
Hidden dependencies, continuity pressure, data custody risk, legacy constraints, and coordination gaps all surface most sharply during transition. The most fragile moments are physical, not virtual.
Successful migrations prioritize clarity, controlled execution, and traceability. They resist the urge to rush and focus instead on maintaining control at every step.
Reconext supports organizations at the point where that control matters most, when systems are moving, assets are being retired, and accountability must be preserved.
If you are planning a data center migration or consolidation, Reconext can help ensure the transition is precise, secure, and accountable.