In data center decommissioning projects, the same reflex comes up again and again: “If it has data, crush it.” Drives shredded. Servers smashed. Assets written off as scrap. It solves one problem and creates three more: financial, environmental, and operational.
That’s the trap of treating secure data destruction as synonymous with physical destruction. Yes, shredding makes data disappear. But it also wipes out hardware value, inflates e-waste, and blocks any chance of recovery or reuse. Industry-wide, thousands of electronic devices are destroyed unnecessarily under blanket “destroy everything” policies, turning what could have been six figures in recovery value into scrap metal.
The smarter definition of secure data destruction is simpler: render sensitive information permanently irretrievable while preserving as much device value as possible. Done right, data becomes unrecoverable, compliance is provable, and hardware lives on through resale, redeployment, or donation.
This guide explains what secure data destruction really means, the certified methods recognized by NIST 800-88 and IEEE 2883, and how to execute the process in a way that protects against data breaches, satisfies legal requirements, and preserves hardware value.
Key takeaway
Shredding servers guarantees one outcome: scrap weight. Meanwhile, certified wiping guarantees two: ESG compliance and recovered value. That’s why we treat wiping as the default, and destruction as the last resort.
Understanding secure data destruction
Secure data destruction means one thing: data no one can get back. Whether it resides on a laptop, a tape, or a rack of solid-State Drives, the test is the same. Zero recovery.
Shredding passes that test, but so does wiping. The difference? Shredding destroys value, wiping preserves it. One costs you money, the other returns it.
Why it matters:
- Security → breaches cost millions and trigger audits.
- Compliance → serialized proof is required to satisfy HIPAA, GDPR, PCI DSS, and more.
- Sustainability → every drive you wipe instead of shred avoids e-waste and carbon.
If the goal is to protect data, there’s no reason to sacrifice hardware that could still generate value.
Why secure wiping is better than destruction

For years, the default answer to secure data disposal was simple: shred everything. If a device could hold information, it went straight to the crusher. That reflex is easy to understand. When the cost of a data breach can run into millions, no one wants to take chances. But shredding, while dramatic, isn’t the only way to make data irretrievable.
Secure wiping achieves the same outcome without the collateral damage. Reconext engineers on large decommissioning projects regularly see over 90% of qualifying assets cleared for resale after certified wipes. Instead of a pile of shards, enterprises recover value, keep hardware in circulation, and meet compliance obligations with evidence in hand.
The benefits extend well beyond revenue:
- Environmental gains → Extending a server’s life avoids the carbon footprint of new production and keeps hazardous materials out of landfill.
- Operational intelligence → Failed drives reveal supplier weak points and usage trends — insights you lose forever if everything is shredded.
- Audit defense → Serialized certificates aligned to NIST 800-88 and IEEE 2883 standards provide defensible proof in front of regulators and boards.
Some devices will still require destruction, such as failed drives, policy-bound categories, or equipment damaged beyond repair. But those are edge cases. The rule is simple: wipe whenever you can, destroy only when you must.
Key data destruction methods
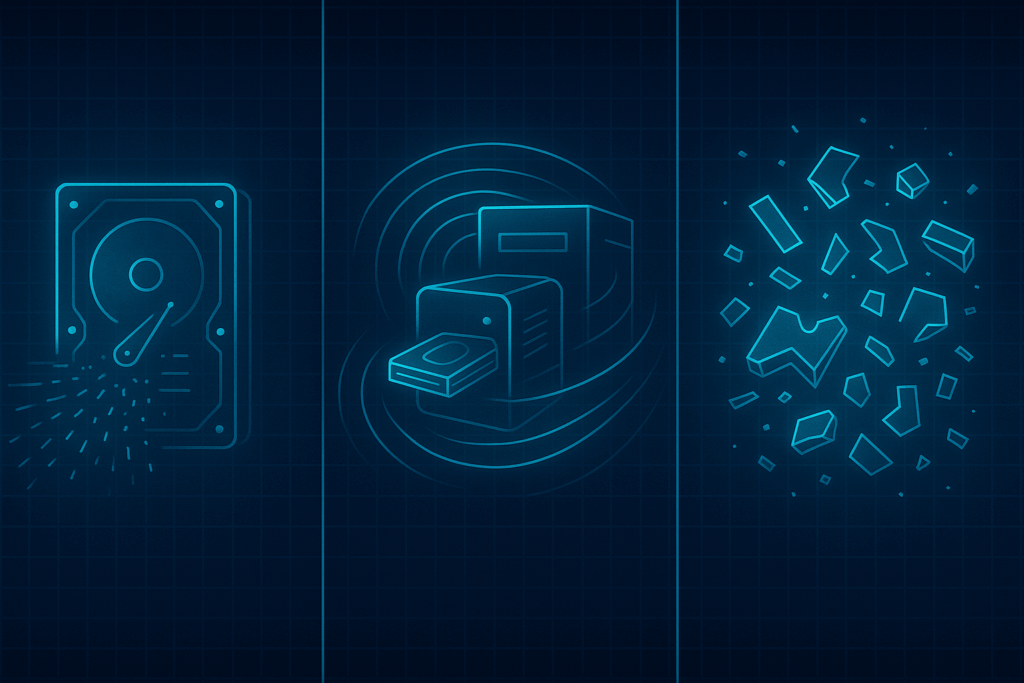
Once you get past the shred-everything reflex, the real question is: which method makes the most sense for each device? Different media demand different approaches, and the right choice determines whether you recover value or reduce everything to waste.
- Data Wiping (Software-Based Sanitization) The gold standard for functional drives and systems. Certified software overwrites storage media with multiple passes until the original is permanently irretrievable. Devices remain usable for resale or redeployment. Standards like NIST and IEEE recognize wiping as compliant sanitization, provided there’s serialized reporting. Reconext’s Proteus platform wipes dozens of drives at once, tying each certificate back to individual serials.
- Degaussing (Magnetic Field Erasure) For magnetic storage like HDDs and tapes, degaussers scramble magnetic domains with a high-powered pulse. It’s effective but renders devices unusable, so resale value is lost. SSDs and flash aren’t affected. In tightly controlled industries, degaussing is sometimes paired with destruction when wiping isn’t possible.
- Physical Destruction Shredding, crushing, or pulverizing leaves no room for recovery or reuse. Necessary for failed devices, damaged hardware, or contracts that demand it. But it’s the costliest route long-term because it eliminates every ounce of resale or redeployment potential.
Bottom line: Wiping preserves value, degaussing has niche use, and destruction is the fallback.
Choosing the right method
Every data-bearing device needs a decision: wipe, degauss, or destroy? The mistake most companies make is applying one answer to everything. That’s how functional hardware ends up in a shredder and compliance gaps open when the wrong method is used.
The smarter approach is a sequence:
- Identify the media → HDDs/SSDs = wipe; tapes = degauss or destroy; flash/optical = wipe if supported, destroy if not.
- Check the condition → working drives can usually be wiped; failed drives move to destruction.
- Account for policy → some industries write destruction into contracts; most follow NIST 800-88, which allows certified wipes.
- Execute and verify → proof is mandatory. A wiped drive isn’t secure without a certificate. A destroyed drive isn’t defensible without custody records.
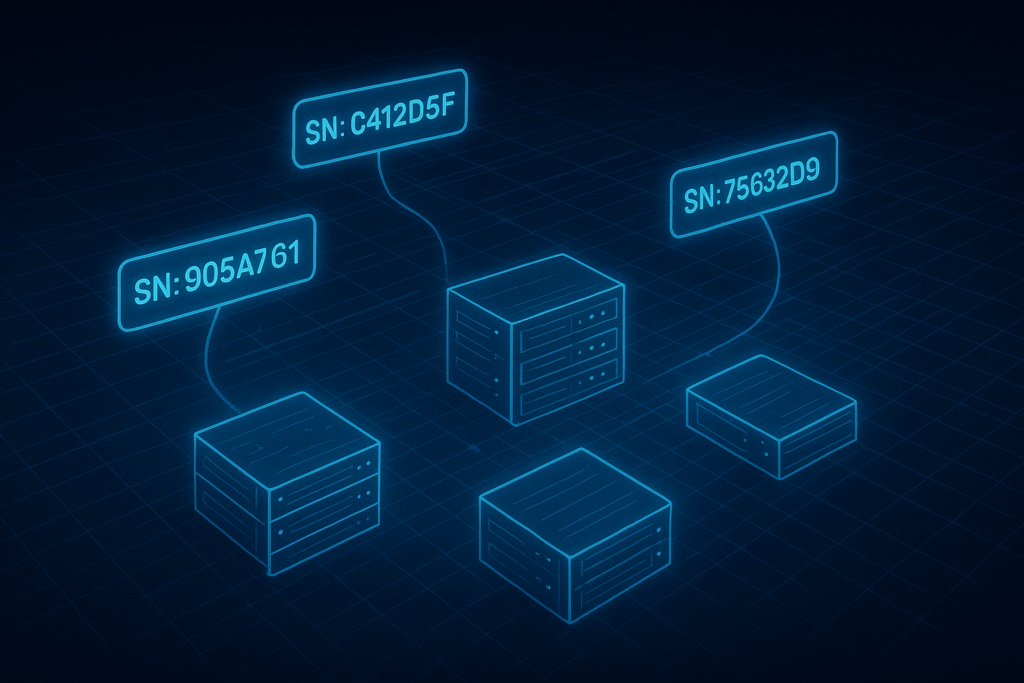
Certified wiping and resale services
Making data irretrievable is only half the job. The other half is proving it. Regulators and boards don’t want assurances. They want evidence.
A certified process ties every action to a device. Each hard drive, SSD, or server is logged by serial number, processed with a recognized method, and issued a unique certificate. That certificate becomes part of the audit trail, matched against the inventory, and stored for future proof. Without it, you don’t have compliance. You have liability.
Reconext’s platforms are designed for scale:
- Proteus → portable, asynchronous erasure across 32- or 64-bay testers. Each drive logged individually, with error handling and command-level reporting.
- Rackwipe → network-boot wiping across entire racks. Instead of pulling drives and wiping them one by one, racks are cleared in parallel, with serialized certificates for every unit.
Because these systems link directly to resale and redeployment channels, sanitization and value recovery happen in the same workflow. Data is destroyed, proof is generated, and devices move straight into secondary markets.
Compliance and legal considerations
Regulations don’t care about good intentions. They care about verifiable outcomes. If you can’t prove data is irretrievable, you have exposure.
Key obligations:
- HIPAA → requires patient medical records and other sensitive data be irretrievable, with certificates to prove it. Penalties: up to $50,000 per violation.
- GDPR → demands proof that EU personal data is erased at end-of-life. Fines: up to 4% of global revenue.
- PCI DSS → mandates sanitization and secure disposal for payment card systems. Breaches trigger fines and remediation.
- GLBA → governs U.S. financial institutions, requiring secure handling of customer information throughout lifecycle.
What’s common: proof beats promises. Regulators expect certificates tied to serials, with timestamps, method, and operator recorded. Custody logs must show how assets moved without blind spots.
Reconext’s wipes are audited against NIST 800-88 and DoD 5220.22-M and validated under ADISA (IEEE-aligned) reviews at the command level. That scrutiny ensures forensic resilience: even when customers bring in recovery teams, data remains unrecoverable.
Environmental responsibility

Data destruction decisions carry environmental weight. Every server shredded prematurely adds to the 50+ million tons of e-waste generated annually, much of it never properly recycled.
Drives and servers contain lithium, lead, mercury, and brominated plastics, which hazardous if mishandled. They also contain valuable metals and rare earths. Destroying hardware before its time means repeating mining and manufacturing sooner, with all the carbon that entails.
Certified recycling frameworks — R2v3, e-Stewards, ISO 14001 — control downstream handling. They ensure hazardous fractions are contained, valuable materials reclaimed, and nothing exported illegally. But recycling should be the last resort, not the first reflex.
Resale and redeployment are the most sustainable outcomes. Every wiped and reused device avoids landfill, extends lifecycle, and reduces Scope 3 emissions. For enterprises under ESG pressure, those extensions translate directly into measurable impact.
A wiped server isn’t just secure. It’s circular.
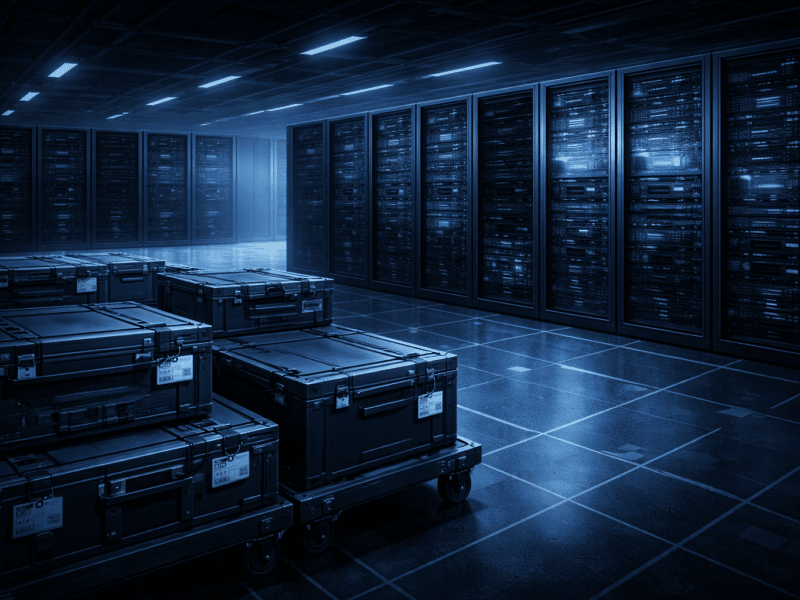
Best practices for secure data destruction
To make data destruction both compliant and value-conscious, follow five fundamentals:
- Keep a complete inventory → track every asset from pickup to final disposition.
- Match method to media → HDDs, SSDs, and tapes require different approaches.
- Require certificates → serialized Certificates of Sanitization or Destruction are non-negotiable.
- Prioritize reuse → wipe and redeploy before recycling or destroying.
- Vet providers carefully → look for ISO, R2v3, and ADISA certifications, and review audit trails.
If you wouldn’t trust your family photos to a random repair shop, don’t trust enterprise data to someone with a hammer and a shredder.
Conclusion
Secure data destruction is about erasing information, not destroying devices. With certified wiping, enterprises can:
- Protect sensitive data falling into the wrong hands.
- Prove compliance with industry regulations and auditors.
- Recover hardware value.
- Reduce environmental impact.
At Reconext, this isn’t exceptional work. It’s routine. And in this field, boring is the highest compliment you can get.
Ready to stop shredding your value? Talk to Reconext about secure, resale-first data destructions and IT Asset Disposition services.