$4.44 million. That is the average cost of a data breach according to IBM’s 2025 Cost of a Data Breach Report. Your organization is likely to suffer a loss, whether small or large, if you dispose of retired IT assets without first performing proper ITAD data sanitization.
The good news is that the $4.44 million figure marked the first decline in five years, indicating that organizations are starting to take data sanitization seriously. However, the challenges of doing it right, what to avoid, and how to choose a vendor remain.
That is why in this article, we help you understand the best data sanitization methods, best practices, and a proven framework for choosing your next ITAD provider.
Key Takeaways
- Effective ITAD data sanitization starts with the right method for the right device. HDDs, SSDs, and high-risk assets do not all require the same approach, and using the wrong one can leave recoverable data behind.
- Data sanitization should be built into your ITAD process, not treated as the final cleanup step. A documented policy, chain of custody, verification, and the right ITAD partner help you reduce breach risk while still protecting resale value, compliance, and sustainability goals.
What Is ITAD Data Sanitization?
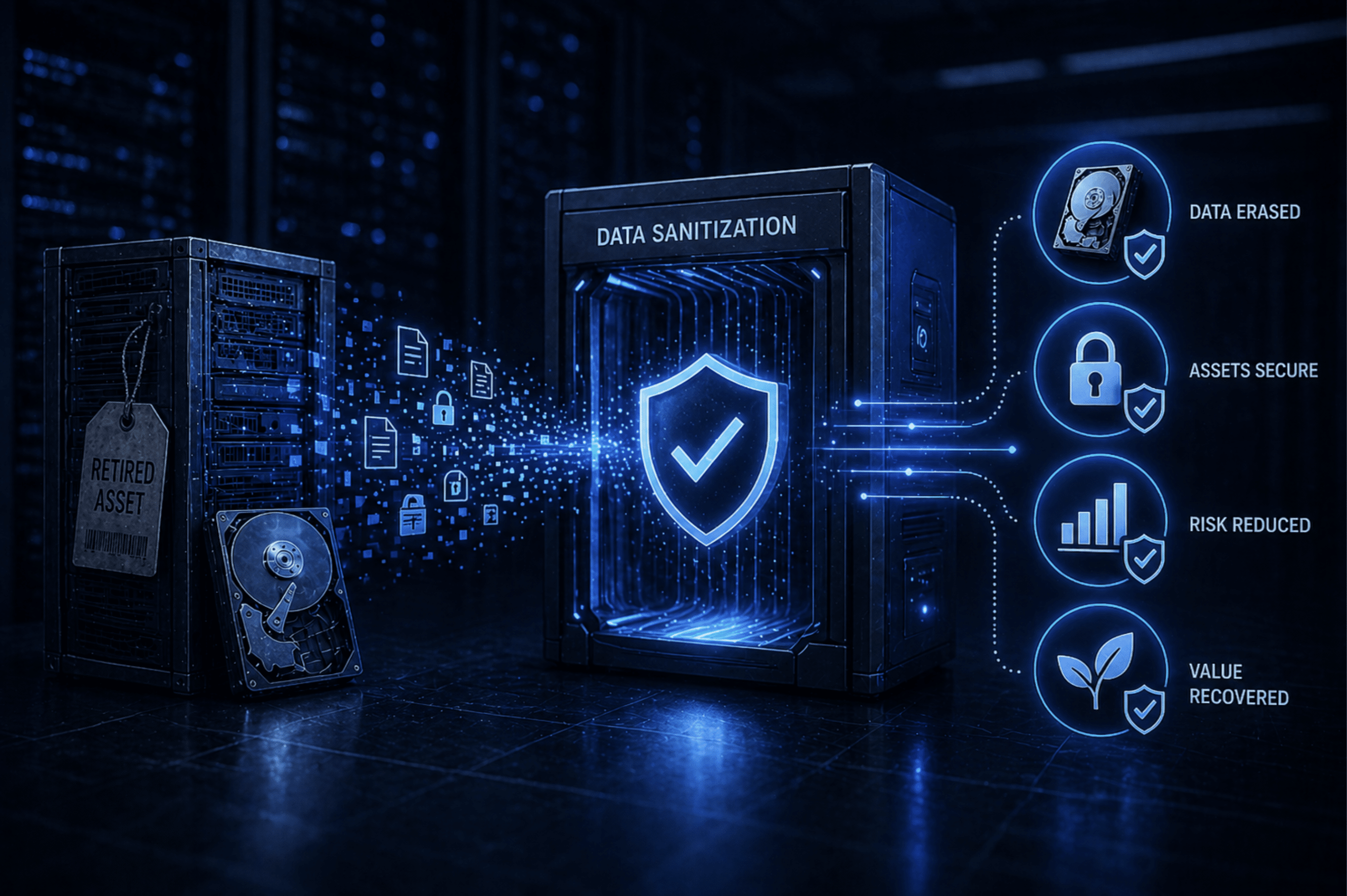
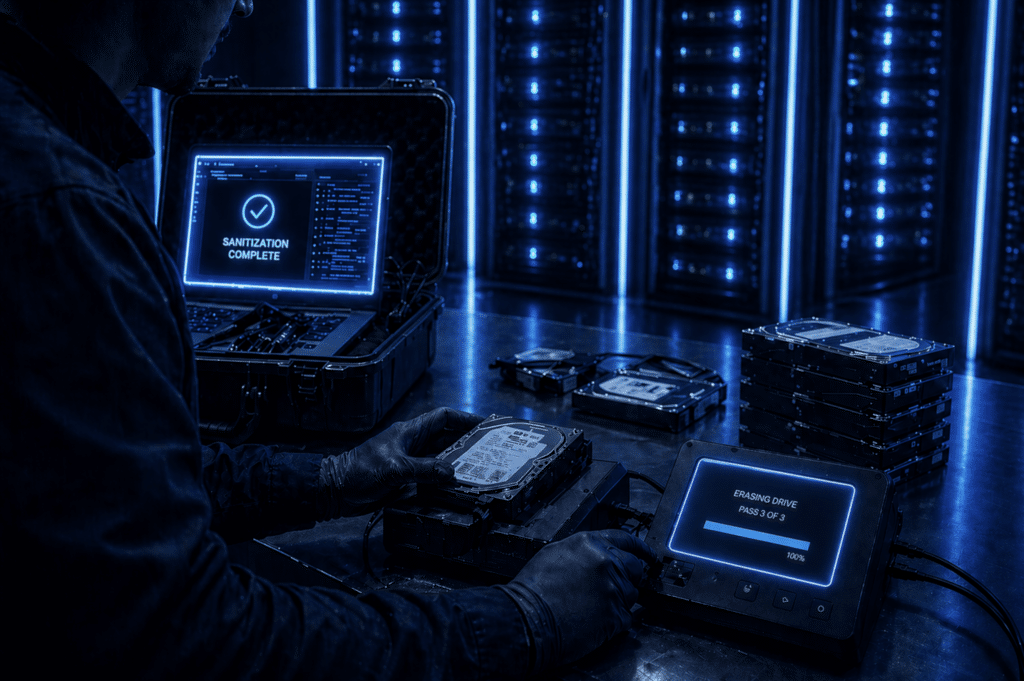
ITAD data sanitization is the process of permanently and irreversibly erasing data from storage devices before they are recycled, reused, or resold. The goal of this process is to ensure that sensitive data cannot be recovered once the devices are no longer under the original owner’s custody.
Typically, your organization starts the ITAD data sanitization process once devices are no longer in active use. Or at least it should: most organizations wait until devices have piled up in storage before wiping their data.
ITAD data sanitization works best when it’s treated as a proactive, not a reactive, process. In other words, you need an ITAD strategy that dictates how and when storage media is completely cleared.
The data sanitization strategy you develop also helps you create policies, best practices, chain-of-custody rules, and more. Without these, retired devices could be resold before complete data removal, stolen, or wiped using the wrong data sanitization standards.
When done right, data sanitization can support your environmental sustainability and value recovery goals: you could be leaving value on the table by using unsuitable data sanitization methods or throwing away reusable devices. To avoid losing device value, always work with professional ITAD service providers to customize sanitization strategies tailored to your needs.
Common ITAD Data Sanitization Techniques
Under the NIST SP 800-88 guidelines, media sanitization is classified into three main levels: clear, purge, and destroy. The following ITAD data sanitization techniques are derived from these three levels.
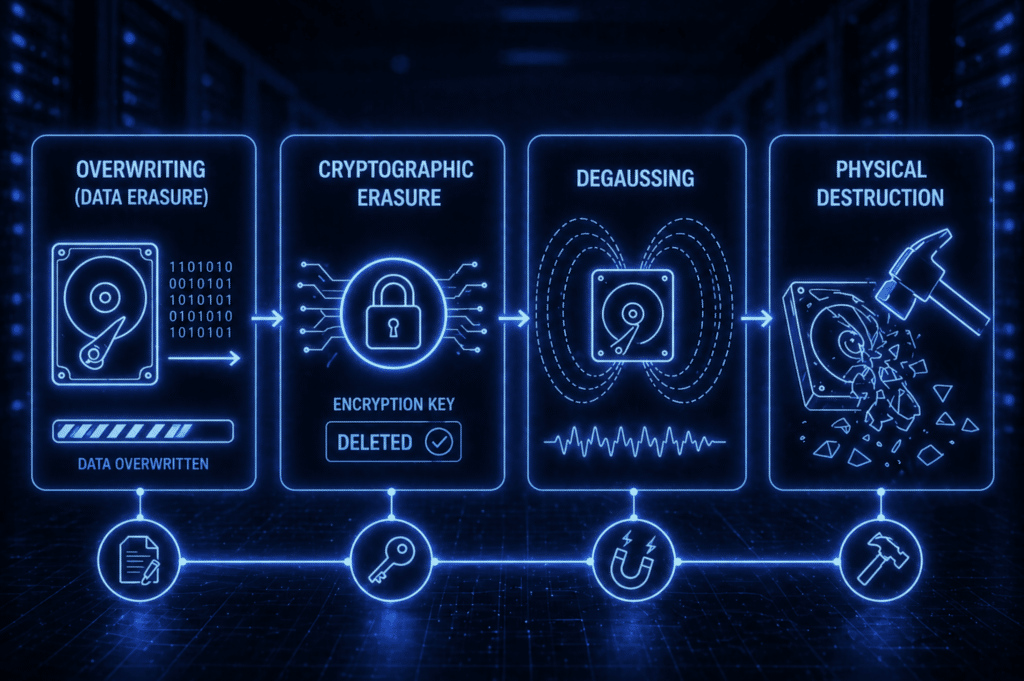
Overwriting (Data Erasure)
Overwriting is a standard data wiping process that uses software to literally overwrite existing data with new random patterns of 0s and 1s. Data erasure is another name for overwriting.
This technique is used mostly for traditional, simple magnetic hard drives. In these devices, the software overwriting replaces the old magnetic pattern and completely deconstructs the data. This effectively makes the data unrecoverable.
In modern SSDs and flash storage, overwriting does not guarantee that old data is completely overwritten.
The system may write the new data to the same logical address, while the SSD stores it in a different physical memory cell. That means the old data may still be temporarily stored on the device, even though the operating system no longer points to it. This is why crypto erase exists.
Cryptographic Erasure
For modern storage devices like SSDs, cryptographic erasure is the solution. Think of it as a more advanced version of overwriting, but this time, the data is completely unrecoverable.
Cryptographic erasure encrypts data and deletes the encryption key. That key is essentially the access password for the content, and without it, the encrypted data cannot be accessed. This is a secure data destruction technique that could help destroy data securely.
Degaussing
This technique uses a strong magnetic field to scramble or erase magnetic data on a storage device. It is an older method that primarily works with floppy disks, tapes, and hard drives.
To understand how this method works, you first need to know how data is represented in those types of devices. In an HDD that stores data as magnetic patterns, a degausser uses a strong magnetic field to scramble the patterns. Once this is done, the data is effectively destroyed.
Physical Destruction
Physical destruction methods are self-explanatory: the storage device is destroyed together with its data. While this is not the most sustainable method, it gets the job done. You might also consider it if you are dealing with highly sensitive data to ensure absolute destruction.
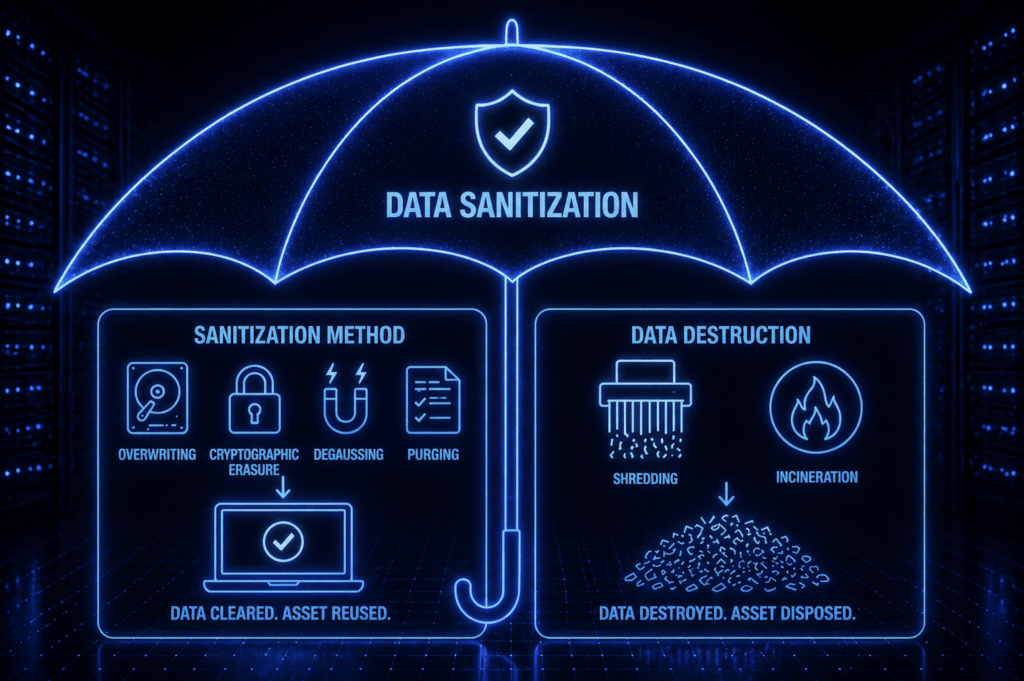
ITAD Data Sanitization vs. Data Destruction
These two phrases are used interchangeably in the industry, but they are not synonyms. Data sanitization is the umbrella term, while data destruction is a subset of it.
As described earlier, data sanitization is a comprehensive process. Think of it like the broader objective of ensuring data is safely erased. Conversely, when people talk about data destruction, they are describing a specific method of asset disposition.
Data destruction involves physical methods, such as shredding or incineration, to destroy devices that contain sensitive data. This is the recommended method if you want to permanently delete highly sensitive data or dispose of unusable assets.
Data sanitization is a more sustainable ITAD strategy. For instance, purging makes devices remarketable and reduces waste.
When choosing between the approaches, consider the device’s working condition, type of data it contains, and its recoverable value. These will help you decide if keeping the device is safe or monetarily reasonable.
Why Data Sanitization Matters in ITAD
The liabilities of data breaches stretch beyond financial losses. Trust is broken, lawsuits are filed, value is lost, and your reputation is on the line. This is what happens when you ignore data security. The upside is that the benefits are equally as large.
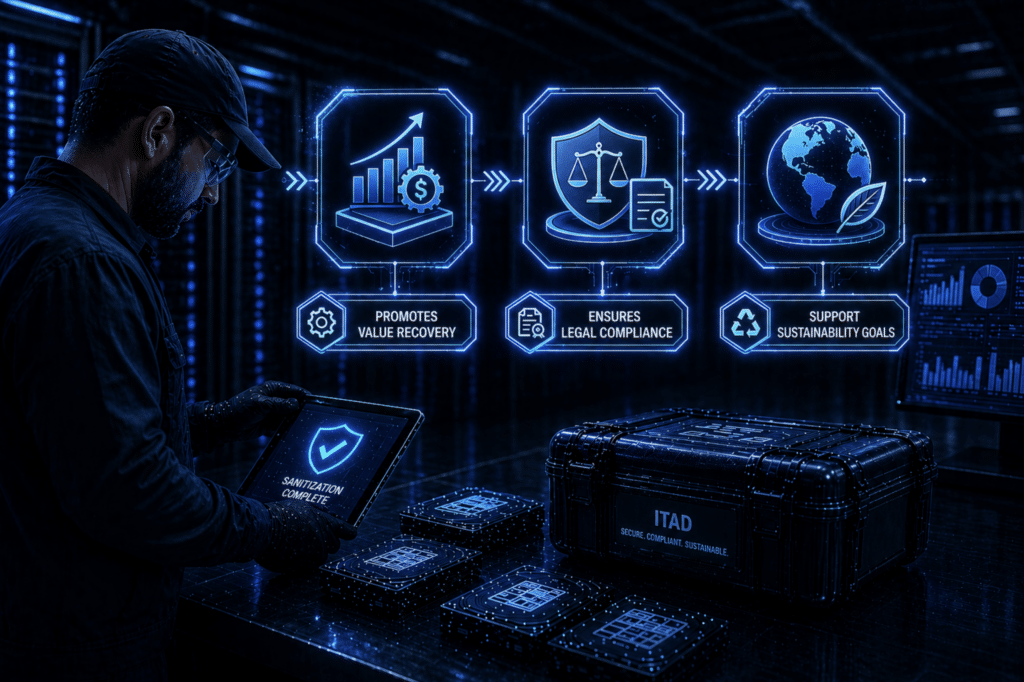
Promotes Value Recovery
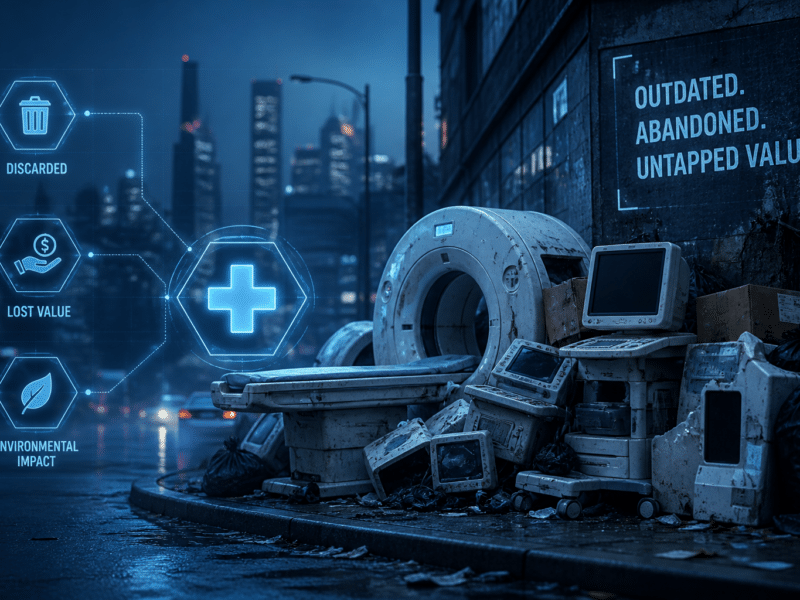
Companies that default to destroying devices are leaving money on the table. Consider that such equipment contains valuable materials that could be harvested and recycled for parts.
Securely erasing data in these devices and sustainably recycling them can recover up to a third of their original value.
Part of the original value of devices can also be recovered through remarketing. In this case, usable devices are repaired and refurbished and sold to secondary markets. Items like mobile devices and computers recoup up to three-quarters of their original value. Data sanitization methods, such as purging, help recover value by restoring devices to factory settings.
Ensures Legal Compliance
There are several organizations that safeguard Personally Identifiable Information (PII), especially in sensitive industries like healthcare. These organizations create policies, such as HIPAA and NIST SP 800-88 R2, that you must follow when choosing media sanitization methods.
Data sanitization is recommended because the process creates paper trails that can be audited to demonstrate regulatory compliance. Documents such as the certificate of deconstruction (CoD) can be used to show that the data erasure process was successful.
Support Sustainability Goals
E-waste is projected to reach 82 million metric tons by 2030. This comes even as major industry players plan to reach carbon neutrality in the same year. Without sustainable ITAD practices, achieving these goals might be difficult.
Data sanitization is among the best bets for reaching these goals. Global ESG regulators know this, and they actively incentivize you to take up responsible recycling and other sustainability practices that reduce e-waste.
ITAD Data Sanitization Best Practices
Data sanitization done right has several financial and environmental benefits. The doing-it-right part is where most organizations skip steps and end up with liabilities.
As such, we have gathered the best practices from our own experience and the ITAD industry at large to help you get it right. Here is what you need to be doing:
- Create a formal data sanitization policy: Policies define the procedures, roles, and responsibilities governing the secure destruction of data. If your policy aligns with guidance from the National Institute of Standards and Technology, you have the perfect blueprint for data destruction.
- Establish a documented chain of custody: You need a traceable record of retired assets from the moment they leave your facility until they are destroyed or remarketed. A clear chain of custody helps avoid data breaches during handling and transport.
- Stick to the recommended sanitization techniques: Always choose among cryptographic erasure, data erasure, degaussing, or physical destruction. Other methods might work, but they won’t be as effective at completely erasing data.
- Always verify that sanitization is complete: However close you are with your ITAD provider, do not take their word for it. Verification processes should include a certificate of deconstruction to confirm that the work was completed.
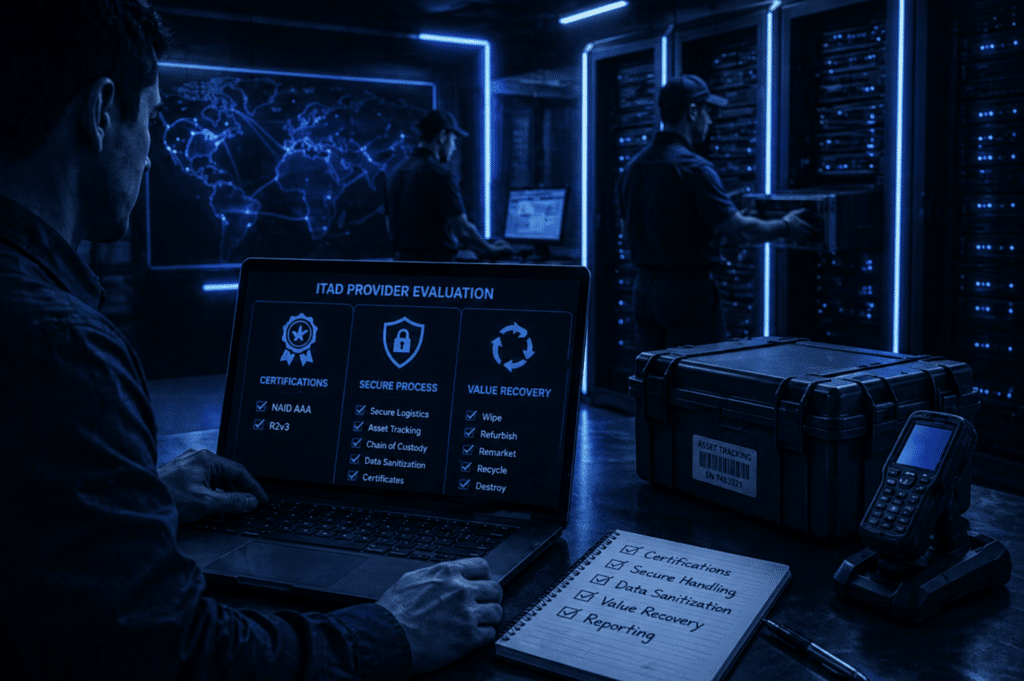
- Work with certified ITAD professionals: Most certified ITAD professionals guarantee safety, value recovery, and auditable ITAD processes. Therefore, always verify that your ITAD provider has at least NAID AAA and R2v3 Certifications.
Other best practices your organization could adopt include training your staff on security awareness and regularly auditing your ITAD policy. Technology is constantly changing, and you need to adapt to it to apply the most suitable data protection methods at all times.
How to Choose an ITAD Provider
Choosing an ITAD partner for your organization could be a highly rewarding process if you do it right. There is no shortage of vendors in the market, but the choice you make will determine how well you sanitize data.
Start with certifications. Your provider should have NAID AAA and R2v3 certifications. These prove that the vendor follows audited processes for secure handling, erasure, destruction, recycling, and downstream vendor control.
Next, look at how they handle the assets. A reliable ITAD provider should offer secure logistics, serialized asset tracking, documented chain of custody, onsite and offsite service options, and device-level reporting. You should also ask how they verify sanitization, which method they use for each device type, and what certificate they provide after completion.
Then, make sure they prioritize value recovery. The right provider should help you decide which devices can be wiped, refurbished, remarketed, recycled, or destroyed.
If you want to skip the evaluation criteria and elevate your IT asset disposition program today, choose Reconext. With decades of industry experience, Reconext has mastered secure ITAD across major industries.
From data sanitization and chain-of-custody control to repair, refurbishment, recycling, and remarketing, Reconext helps you protect sensitive information, recover more value, and retire IT assets with confidence. Contact Reconext today.
FAQs
Does a factory reset completely erase our phones or laptops?
No, a factory reset does not completely erase the data on your phones or laptops. A factory reset removes user access and restores the device’s settings to those shipped with the device. This means the customization is recoverable, making a factory reset a poor choice for data sanitization.
What are the primary data sanitization methods?
The primary data sanitization methods are data erasure, degaussing, and physical destruction. These methods work well across various types of hardware and data and are in line with industry best practices.
Can data be erased and the hardware reused?
Yes, data can be erased and the hardware reused. However, only secure erasure methods can prevent data reconstruction. Methods like encryption make the existing data unrecoverable and the hardware reusable.